Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Veracode Named A Leader In The 2022 Gartner® Magic Quadrant For Application Security Testing For Ninth Consecutive Time
Sysdig achieves AWS DevSecOps specialization within AWS DevOps Competency
Sysdig is pleased to announce that it has achieved Amazon Web Services (AWS) DevOps Competency for development, security, and operations (DevSecOps). This designation highlights the value provided by the Sysdig platform to AWS customers to achieve their DevSecOps goals. As a key partner for the ecosystem, Sysdig collaborates closely with AWS and its customers to enhance the protection of cloud infrastructure and applications against continuously evolving security threats.
SnykCon recap: Automation for better compliance and faster feedback loops
Automation is a key component of DevSecOps because it increases efficiency. Automating work in your software development lifecycle helps you integrate multiple tools into your workflow. It also lets developers, maintainers, and security champions focus on coming up with creative solutions for tough problems, rather than spending time on tedious manual tasks.
Veracode Acquires ML-Powered Vulnerability Remediation Technology From Jaroona GmbH
On the heels of our significant growth investment from TA Associates, we are pleased to announce our acquisition of auto-remediation technology from Jaroona. Jaroona’s intelligent remediation technology accelerates Veracode’s vision and strategy to automatically detect and remediate software vulnerabilities. Jaroona was recognized as a Gartner Inc. 2021 Cool Vendor for DevSecOps.
DevSecOps build and test process
In the previous article about the coding process, we covered developers using secure coding practices and how to secure the central code repository that represents the single source of truth. After coding is complete, developers move to the build and test processes of the Continuous Integration (CI) phase. These processes use automation to compile code and test it for errors, vulnerabilities, license conformity, unexpected behavior, and of course bugs in the application.
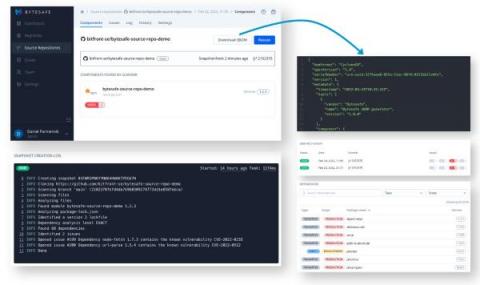
Export and Distribute SBOMs Directly From Your Git Repositories
Guest Blog by Daniel Parmenvik – CEO of bytesafe.dev For many, Software Bill of Materials (SBOMs) have changed from a manual list of assets for due diligence procedures to become an integral and automated part of software development. The ever increasing appetite for open-source software translates into a need to keep track of software assets (or open-source dependencies) for all applications, at any given point in time.
RKVST Set Free
Today we make RKVST available for public use with a free access tier so you can discover what a Zero Trust Fabric can do for you. From tracking software supply chain lifecycles to nuclear waste, RKVST is a powerful tool that builds trust in multi-party processes, when it’s critical to have high assurance in data for confident decisions. But before going all the way you can start simple: tracking software releases and contents with SBOMs.
Shift Left for DevSecOps Success
Not long ago, developers built applications with little awareness about security and compliance. Checking for vulnerabilities, misconfigurations and policy violations wasn’t their job. After creating a fully-functional application, they’d throw it over the proverbial fence, and a security team would evaluate it at some point – or maybe never. Those days are gone – due to three main shifts.
ITOps vs. SecOps vs. DevOps vs. DevSecOps
ITOps, SecOps, and DevOps may sound similar. Indeed, they are similar - to a degree. But they have different areas of focus, different histories, and different operational paradigms. Keep reading for an overview of what ITOps, SecOps, and DevOps mean and how they compare. We'll also explain where DevSecOps fits into the conversation - and why you shouldn't worry so much about defining these terms perfectly as you should about finding ways to operationalize collaboration between your various teams.