Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
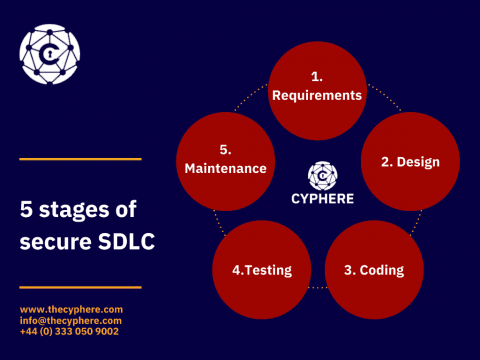
Secure software development lifecycle (SDLC) Best Practices
With all the remote works, online businesses, and digital lifestyle, applications (software) have become an integral part of our lives. In contrast, the growing rate of data breaches and cyber-attacks exploiting minor glitches in application functionality has diverted attention to application security which is still underrated in the era of phenomenal technological advancement.
Device Authority and Intercede distribute SBOMs using RKVST SBOM Hub
DevSecOps deploy and operate processes
In the previous article, we covered the release process and how to secure the parts and components of the process. The deploy and operate processes are where developers, IT, and security meet in a coordinated handoff for sending an application into production.
Mend Explainer
JFrog Connect: Ready for What's Next for DevSecOps, Edge and IoT
Today at swampUP, our annual DevOps conference, JFrog CTO Yoav Landman unveiled the next step toward making the Liquid Software vision of continuous, secure updates a truly universal reality. We’ve introduced JFrog Connect, a new solution designed to help developers update, manage, monitor, and secure remote Linux & Internet of Things (IoT) devices at scale.
Automate Security Workflows in ServiceNow with the JFrog Xray Spoke
In 2022, JFrog and ServiceNow engaged in a series of meaningful conversations around the state of DevSecOps and how the industry could benefit from tighter integrations with IT-Operations tools.
What is DevSecOps? DevSecOps explained in under 7 mins | 2022
DevSecOps 101: Best Practices
Generating an SBOM is just the tip of the iceberg
It has been nearly a year since the President Biden’s Executive Order 14028 catapulted Software Bills of Materials (SBOMs) from niche topic to the forefront of efforts to improve security of cyber supply chains. Since then not only have federal agencies including NIST and CISA delivered significant amounts of guidance and insight, but SBOMs have been the subject of intense debate across developer communities and beyond.