Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vulnerability
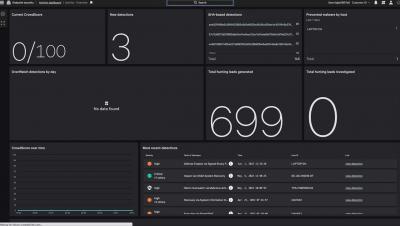
OverWatch Casts a Wide Net for Follina: Hunting Beyond the Proof of Concept
CVE-2022-30190, aka Follina, was published by @nao_sec on Twitter on May 27, 2022 — the start of Memorial Day weekend in the U.S. — highlighting once again the need for round-the-clock cybersecurity coverage. Threat hunting in particular is critical in these instances, as it provides organizations with the surge support needed to combat adversaries and thwart their objectives.
CrowdStrike Falcon Prevents the Follina Zero-day Vulnerability
Vulnerability summary: Follina, CVE-2022-30190
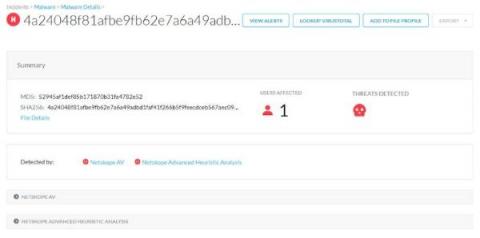
On May 27, 2022, the nao_sec independent security research group shared a VirusTotal link to a weaponized Microsoft Office document revealing a previously unknown vulnerability in the Microsoft Support Diagnostic Tool (MSDT). This vulnerability is most likely to be exploited via phishing lure attachments and is triggered when a document is opened.
Top CVE Trends - And What You Can Do About Them
Cybersecurity awareness, protection, and prevention is all-encompassing. In addition to implementing the right tools and resources, and hiring skilled professionals with the right cybersecurity education and experience, organizations should be aware of the latest CVEs.
CVE-2022-30190: New Zero-Day Vulnerability (Follina) in Microsoft Support Diagnostic Tool
On May 27, 2022, a Microsoft Office document was submitted from Belarus to VirusTotal, using a novel method to deliver its payload. This new technique was identified as a Zero-Day RCE (Remote Code Execution) vulnerability in Microsoft Support Diagnostic Tool (MSDT), which is now being tracked as CVE-2022-30190. As of this writing, it affects only Windows computers running with MSDT URI protocol enabled.
NPM Dependency Confusion
CVE-2022-30190 - Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Zero-Day Vulnerability in Windows
RCE à La Follina (CVE-2022-30190)
If you want just to see how to find detections for the Follina MS Office RCE, skip down to the “detections” sections. Otherwise, read on for a quick breakdown of what happened, how to detect it, and MITRE ATT&CK mappings.
Penetration Testing To Prevent API Attack
This blog describes the attack path we have uncovered during a recent penetration test of a web application, coupled with a back-end infrastructure assessment. Throughout we introduce different attack techniques and tools that can be used to attack the underlying infrastructure and APIs of a web application.