Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vulnerability
Follina - CVE-2022-30190
The Log4j Vulnerability is Still Out There: How a Dynamic SBOM Helps You Find It
Despite the time that’s passed between its discovery and today, Log4Shell continues to plague the tech industry. The number of downloads of exploitable Log4j packages has remained consistent, and because it nests itself deep in files, it is often difficult for current tools to find vulnerabilities. A recent report from Rezilion finds that almost 60% of packages affected by the vulnerability remained untouched, and over 90,000 publicly facing servers are still running obsolete versions of Log4j.
A Weaponized npm Package '@core-pas/cyb-core' Proclaimed Pentesting Related
Two packages of well-known origin were found exfiltrating Windows SAM and SYSTEM files, apparently as part of internal security research rather than a targeted dependency confusion attack. On June 6th, 2022, the Mend research team used Supply Chain Defender to detect and flag two malicious packages from the same author that contained identical code. We alerted npm and the packages were removed within three hours of publication.
CVE-2022-25845 - Analyzing the Fastjson "Auto Type Bypass" RCE vulnerability
A few weeks ago, a new version for Fastjson was released (1.2.83) which contains a fix for a security vulnerability that allegedly allows an attacker to execute code on a remote machine. According to several publications, this vulnerability allows an attacker to bypass the “AutoTypeCheck” mechanism in Fastjson and achieve remote code execution. This Fastjson vulnerability only recently received a CVE identifier – CVE-2022-25845, and a high CVSS – 8.1.
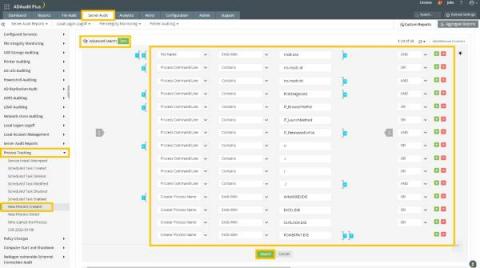
How ADAudit Plus helps you assess your exposure to Follina (CVE-2022-30190)
The recently discovered Windows zero-day vulnerability continues to make news as threat actors across the globe are relentless in their efforts to exploit it. The vulnerability, dubbed Follina, can be exploited when the Microsoft Support Diagnostic Tool (MSDT) is called by a Microsoft Office application using the URL protocol.
What is a Dependency Firewall? What, Why and How?
In recent years more open source vulnerabilities have been discovered than ever before. This is all part of the natural evolution; it’s what we expect to see as the amount of open source usage grows within organizations. But there’s something that we missed in this equation: while identifying vulnerabilities, organizations haven’t found a way to block unwanted dependencies, which made them vulnerable to attacks like never before.
Trustwave's Action Response: More MSDT Fallout with "Dogwalk"
A zero-day vulnerability has been re-disclosed that is very similar to the Follina zero-day announced last week and is actively being tracked by Trustwave SpiderLabs. The vulnerability was initially publicly disclosed back in 2020 but dismissed by Microsoft, which replied at the time: "We are also always seeking to improve these protections.
Denial of Service Vulnerability in Envoy Proxy - CVE-2022-29225
The JFrog Security Research team is constantly looking for new and previously unknown software vulnerabilities in popular open-source projects to help improve their security posture. As part of this effort, we recently discovered a denial of service (DoS) vulnerability in Envoy Proxy, a widely used open-source edge and service proxy server, designed for cloud-native applications and high traffic websites.
Preventing exploitation of the Follina vulnerability in MSDT
This article provides a synopsis of the Follina exploit and simple steps you can take to mitigate this severe remote code execution vulnerability within Microsoft Support Diagnostic Tool (MSDT). This vulnerability is triggered via common Windows applications such as Microsoft Word and is being actively exploited by known hacking groups.