Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vulnerability
Months Later, Are You Still Vulnerable to Log4Shell?
By Yotam Perkal, Head of Vulnerability Research Researchers here at Rezilion wanted to assess the current potential attack surface of the Log4Shell vulnerability today, 4 months later, now that the dust has settled. We hoped that due to the massive amount of media coverage the Log4Shell vulnerability has received, that the majority of applications have been patched. We assumed finding services that are still vulnerable would be challenging. We were wrong.
Vulnerability Scanning & Vulnerability Management is not Hardening
Vulns Unleashed: dompdf, The Reverse Shell Strikes Back!
What the Heck is Spring4Shell? The 2min Explanation We All Need
As the digital world continues to rebuild after the Log4j hurricane, the threat landscape is once again disturbed by the rumbling of an approaching zero-day storm. After barely recovering from a zero-day dubbed as the worst hack ever encountered, concerns are understandably heightened, and as a result, there are many misconceptions about the severity of Spring4Shell.
CVE-2022-24814- Stored XSS In Directus | Synopsys
This Week in VulnDB - MariaDB, VIM and a look at C++ Vulnerabilities
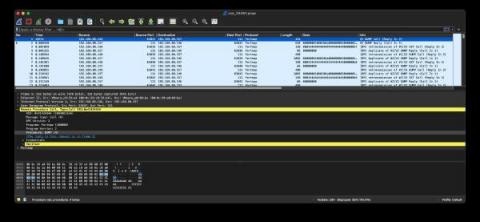
Detecting Windows NFS Portmap vulnerabilities
This month, Microsoft announced two vulnerabilities in portmap, which is part of ONC RPC, on Windows systems. This blog will discuss Zeek detection packages for CVE-2022-24491 and CVE-2022-24497 developed by Corelight Labs.
Preventing cloud and container vulnerabilities
Vulnerabilities are software bugs or weaknesses that could be used by an attacker. They could be present in the operating system, application code, and third-party code dependencies, such as libraries, frameworks, programming scripts, and so on. By taking a secure DevOps approach and identifying vulnerabilities early in development, you avoid frustrating developers with delays when an application is ready for production.
CVE-2022-21449 "Psychic Signatures": Analyzing the New Java Crypto Vulnerability
A few days ago, security researcher Neil Madden published a blog post, in which he provided details about a newly disclosed vulnerability in Java, CVE-2022-21449 or “Psychic Signatures”. This security vulnerability originates in an improper implementation of the ECDSA signature verification algorithm, introduced in Java 15.