Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Compliance
Session 1: The Need for Cybersecurity in U.S. Manufacturing
Session 2: DFARS & CMMC Overview
The 411 on Stack Overflow and open source license compliance
Many of the third-party components we find in audits have been pulled in their entirety from public software repositories (with GitHub being the most popular these days). But with some frequency we also come across snippets—lines of code that have been copied and pasted into source code. They might be a piece of a GitHub project, but they may also have been taken from a blog site like Stack Overflow or CodeGuru.
Data Privacy Update: Virginia Consumer Data Protection Act (VCDPA) in global context
And so it continues. Last month, Virginia passed its own privacy law, the Virginia Consumer Data Protection Act (VCDPA), adding fuel to the fire over a US federal privacy law, and introducing new complexities for businesses operating in or addressing the US market. It will take effect on January 1, 2023 (the same day as California’s CPRA which amends the current CCPA) and was passed in record-breaking time: less than two months, and by an overwhelming majority.
What is a Data Protection Officer (DPO)?
A data protection officer (DPO) is an employee or contractor hired to oversee a company’s data protection strategy and ensure compliance with the General Data Protection Regulation (GDPR). The role was introduced in 2018 to promote compliance with the new laws governing how the personal data of EU citizens is handled. All public authorities are required to appoint a data protection officer to comply with GDPR.
CCPA Compliance: How to Become Compliant
Personal information (PI) enables businesses to customize the customer experience and boost sales. However, consumer rights advocacy and privacy regulations, such as the EU’s General Data Protection Regulation (GDPR) and state data privacy laws enacted in the United States, limit the collection of PI. Preeminent among these laws is the California Consumer Privacy Act of 2018 (CCPA).
What is a managed cloud service?
A managed cloud service handles the complexity of cloud-based IT infrastructure so that in-house teams can continue working towards their business goals. Businesses looking to scale their operations need increasingly sophisticated IT environments. Cloud computing allows teams to do exactly that, yet a decision still needs to be made over who manages the cloud environment; managed cloud service providers fill this gap.
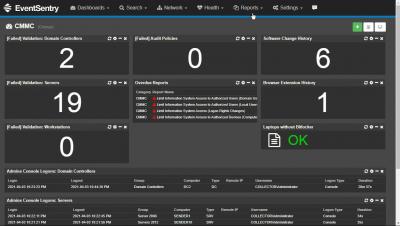
CMMC compliance with EventSentry
What is a Compliance Risk Assessment?
As global regulations for data privacy and cybersecurity continue to proliferate, the pressure for organizations to manage compliance risk grows. To meet the demand for greater compliance risk management and value for corporate stakeholders, compliance professionals must be sure they have a thorough understanding of their compliance obligations and potential vulnerabilities.