Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
June 2022
GDPR Compliance Checklist
ISO 27001 Checklist And Security Controls
Compliance Guide: Third-Party Risk Management and the GDPR
The General Data Protection Regulation (GDPR) is one of the world’s most popular regulations. Though the European Union designed the GDPR to protect European citizens, its compliance transcends European borders, impacting most businesses collecting personal data via their websites - because you can’t control whether a European citizen accesses your website. Third-party vendors often require access to sensitive personal data to deliver their services.
Mobile Devices and CMMC L2
A study recently shared with Ignyte posed a question that has been and is currently on many minds. How are organizations that have to adhere to CMMC level 2 handling personal devices? In other words, how do various device policies such as bring your own device (BYOD), choose your own device (CYOD), company owned personally enabled (COPE), and company owned business only (COBO) work with CMMC requirements.
DFARS Compliance in Microsoft 365
Cybersecurity has become an important topic for the defense supply chain. The ever-increasing number of digital channels that data can be exchanged through, has exponentially increased the risk of data breaches and leaks. This puts a lot of pressure on these organizations to ensure that the risks associated with the handling of sensitive data are as low as possible.
IoT and the GDPR - How to stay compliant
Businesses that incorporate Internet of Things (IoT) into their daily operations have rarely, if ever, had access to so many resources to help improve your customer reach, collect more personal data and reduce your internal operational expenses due to IoT automation. IoT devices are ubiquitous, and as technology advances, so does the invention and use of connected devices within workplaces and our homes.
Navigating New Cybersecurity Policies and Regulations: What You Need to Know
2022 has brought in tighter cybersecurity restrictions and privacy regulations around the world. With the escalation of cyber threats due to the accelerated digital transformation and the Russian invasion of Ukraine, governments globally have made decisions to step up their cybersecurity defense and introduce new measures to protect businesses or national security.
What Is ITAR Compliance? Who Does It Apply To?
The term “ITAR compliance” is a misnomer. Unlike FedRAMP and other compliance frameworks, there is no formal “ITAR Compliance” or “ITAR Certification” process. Organizations that fall under ITAR need to understand how the regulations apply to them and set up internal policies and controls to protect ITAR technical data. Let’s examine what ITAR is all about, and how Keeper’s cybersecurity suite can help you comply with it.
Compliance Guide: 23 NY CRR and Third-Party Risk Management
The NY CRR 500 legislation was instituted by the New York Department of Financial Services (NYDFS) in 2017 in response to the rising trend of cyberattacks in the finance industry. Sometimes regarded as the GDPR for financial services, the NY CRR 500 has a very high standard for sensitive data protection, requiring protection strategies for ensuring the confidentiality, integrity, and security of information systems and nonpublic information (including customer data).
Introducing NC Protect's New CUI Designator Labelling Capability for US Defense Requirements
Protecting Controlled Unclassified Information (CUI) is a top priority for companies that have government and defense contracts, especially with the changes being rolled out in CMMC 2.0. We’re pleased at announce a new NC Protect watermarking feature to support CUI Designator labelling capability to assist US Defense and the Defense Industrial Base (DIB) with meeting the new CUI document handling and tagging requirements. The feature will be globally available during the July 2022 timeframe.
New CERT-In Guidelines: What Does That Mean For You
An organization’s security protocols are vital to maintaining transparency, compliance with government regulations, and trust with customers. On April 28, 2022, the Indian Computer Emergency Response Team (CERT-In) released updated directions for compliance requirements for all India-based companies and organizations with Indian clients.
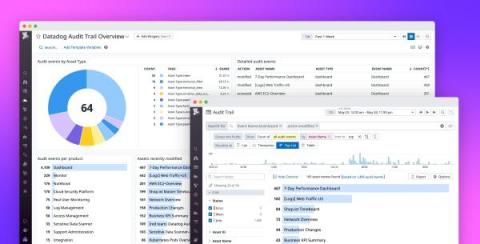
Ensure compliance, governance, and transparency across your teams with Datadog Audit Trail
In order to maintain compliance, enforce governance, and build transparency, teams across your organization need deep insight into how their users and automation interact with Datadog. For stakeholders in leadership roles, such as CIOs and CDOs, knowing what actions users took and when is essential for spotting gaps in enablement, budgeting, and reporting, as well as building a modern compliance strategy for the organization as a whole.
What Is ISO/IEC 27017?
More than a third of organizations suffered a serious cloud security incident in 2021. According to a survey of 300 cloud professionals covered by BetaNews, 36% of those respondents said that their organizations had suffered a severe cloud security data leak or breach in the past 12 months. Looking forward, eight in 10 survey participants said they were worried that they were vulnerable to a data breach related to a cloud misconfiguration.
9 Ways Trust Accelerates Revenue
No matter what niche your organization specializes in, building trust with your customers is a major pillar around which a business is built. In a world where customers are picky with who they work with, data security and privacy practices are quickly becoming a competitive advantage. Showing your customers that you take your regulatory and contractual obligations seriously goes a long way in earning their trust, while also reducing exposure to risk and liabilities.
What Are the Four Main HIPAA Rules?
Is my business email HIPAA compliant?
According to a report published by the FBI Internet Crime Complaint Center (IC3), losses resulting from attacks against business emails are 64 times more damaging than ransomware when measured by dollar amount losses. Phishing and email data breaches can be particularly damaging in the health sector. Regulatory authorities and oversight bodies are incredibly stringent when enforcing compliance measures designed to protect sensitive medical and patient data.
Best Practices of Cybersecurity in Fintech
Fintech, short for ‘financial technology, is the application of new technological advancements to products and services in the financial industry. The Fintech industry is rapidly evolving, driven in part by the adoption of new technologies such as artificial intelligence and blockchain-powered assets. Currently, the Fintech market is projected to reach $190 billion by 2026, growing annually by 13.7%.
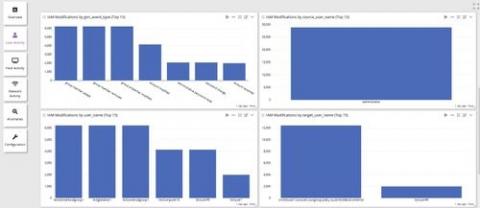
Spotlight on Technology - Governance, Risk & Compliance
PCI DSS 4 0 Requirements Explained
Pillars of Amazon Web Services: Security, Identity, and Compliance
As more and more businesses adopt cloud computing services for their operations, the threat against cloud infrastructure is also increasing. AWS, the huge cloud service provider in the market, provides many security features to secure the cloud structure and customer data. It is essential to understand the service provider’s security policy before adopting it for the business.
CMMC 2.0: key changes
Since my previous blog CMMC Readiness was published in September 2021, the Department of Defense (DoD) has made modifications to the program structure and requirements of the Cybersecurity Maturity Model Certification (CMMC) interim rule first published in September 2020. CMMC 2.0 was officially introduced in November 2021 with the goal of streamlining and improving CMMC implementation.