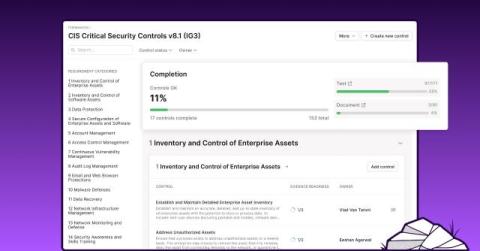
Introducing new Vanta capabilities to automatically improve your security posture
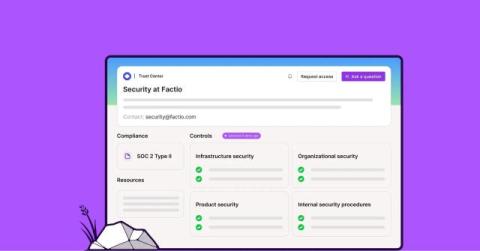
From day one, Vanta has helped security teams build and maintain a strong security posture to protect sensitive data and reduce business risk. Our industry-leading trust management platform provides automated, continuous compliance, ensuring that the necessary people, processes, and technology for strong security are in place and working effectively. With Vanta, customers like Unleash and Pigment are able to reduce costs and free up resources for strategic security initiatives.