Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SIEM
The latest News and Information on Security Incident and Event Management.
SIEM as a Service
SIEM-as-a-Service (SaaS) and Managed SIEM services have gained popularity among companies aiming to meet security compliance standards in a cost-effective manner. Let’s see why a SIEM service can transform your small or mid-sized business’s cybersecurity.
Cost-effective Managed SIEM Service
Contract with a third-party for managed SIEM services is increasingly affordable and requested by all-size organizations. Without any doubt, the advantages associated with this service allow monitoring, analyzing, and responding to cyber security threats more cost-effectively. However, what is a managed SIEM precisely? Is the price the only feature to take into account? What is the difference between a managed SIEM Provider (MSP) and a Managed Security Service Provider (MSSP)?
Elastic achieves Approved Product status from AV-Comparatives
Many organizations consider the AV-Comparatives' test series a standard of quality and a guarantee of a reliable product. Recently, Elastic participated successfully in the AV-Comparatives’ Enterprise Main Test Series and received the Approved Product award. This prestigious and industry-recognized quality award means that the Elastic Security software has been rigorously checked to ensure that it will perform its intended task competently.
Elastic Security 8.1: Stop novel attacks in their tracks
With the release of Elastic Security 8.1, enhance defenses against novel attacks like Log4Shell and prevent adversaries from compromising macOS systems. Achieve visibility into host-based network activity, leverage new sources of threat intelligence, collect data from across your enterprise, and more. Let’s jump in.
PHOREAL malware targets the Southeast Asian financial sector
Elastic Security discovered PHOREAL malware, which is targeting Southeast Asia financial organizations, particularly those in the Vietnamese financial sector. Given the continuous pace of malware development, it's no surprise that adversarial groups will leverage successful campaigns as the basis of developing future attacks, and the recently discovered backdoor campaign targeting Vietnamese financial services is no exception.
One SIEM is not enough?
The idea behind the SIEM (and now XDR!) technologies was to provide a single engine at the heart of the SOC, aggregating data, enabling analytics and powering workflow automation. The SIEM would act as one place to train analysts and integrate a range of complementary technologies and processes. Given the efficiency that comes from centralization, I was surprised to hear that a growing number of defenders are actually using two SIEMs. Why is that?
Micro Lesson: Entity Normalization with Lookup Tables
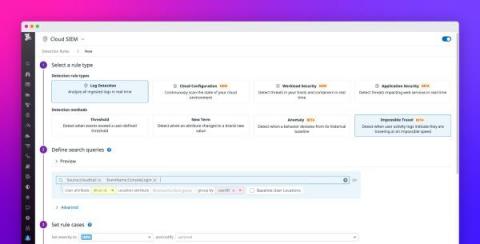
Detect suspicious login activity with impossible travel detection rules
Many modern applications are regularly accessed by countless users from all over the world, which makes it difficult to identify anomalous patterns in login activity indicative of a security breach. This challenge is compounded by the fact that people travel often and regularly access their accounts from new locations. To detect this common attack vector, the Datadog Cloud SIEM now provides the impossible travel detection rule type which helps you spot suspicious logins with confidence.
Elastic protects against data wiper malware targeting Ukraine: HERMETICWIPER
Recently, we have seen several malware campaigns attacking Ukrainian organizations — Operation Bleeding Bear is a recent one of note. Elastic Security researchers recently verified a data wiper malware campaign that is targeting Ukrainian systems. As this malware campaign is new, with more information being uncovered hourly, it is being referred to as HERMETICWIPER.