Inside the war room: Best practices learned from the Sumo Logic security incident
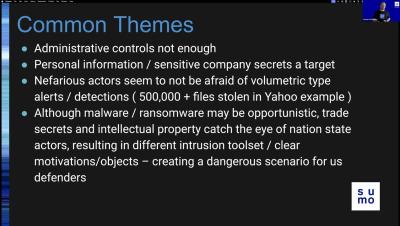
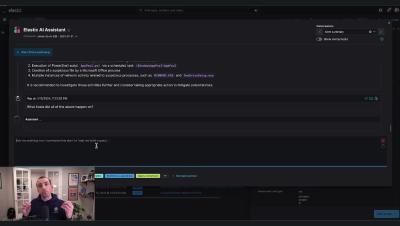
In November 2023, Sumo Logic experienced a security incident. While no one wants to be a victim of a cyberattack, and we certainly learned a lot about things that we can do better in the future, our team was lauded by customers and media alike for how we handled the situation underscoring the importance of a good incident response plan. One of the core values at Sumo Logic is that we’re in it with our customers. But more broadly speaking, we’re in it with the InfoSec community.