Observability Point Tools or Platform-Based Observability?
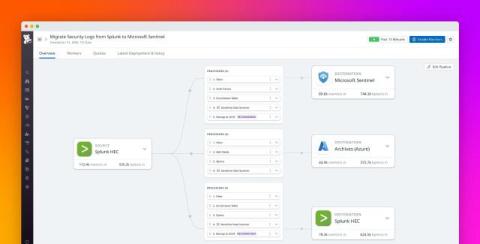
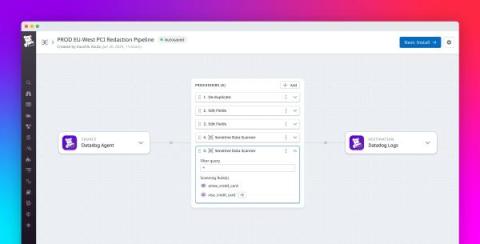
Observability pipelines help cybersecurity teams maximize the value of their data by giving them critical visibility into telemetry. This visibility allows them to eliminate visibility gaps, enhance security operations center (SOC) efficiency, and reduce spending on high-cost SIEM tools. Until recently, the observability space has been dominated by point solutions like Cribl, Monad, and Observo.