Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Arctic Wolf Offers Canadian Rural Healthcare Network Holistic Security Support
As a rural healthcare network located north of Toronto, Ontario, the employees of Grey Bruce Health Services understand that PHI fetches a high value on the dark web, and that they could be one ransomware attack away from stolen data, or worse, encrypted networks that prevent critical patient care. With Arctic Wolf, including Arctic Wolf Managed Detection and Response and Arctic Wolf Managed Risk, IT Director Liane Coates feels confident and comforted that there’s a protective defensive layer not only monitoring the environment 24x7 but working on vulnerability management and proactive security strategies.
Demo Tuesday
What happens when you are the sole subject matter expert on a part of the network, and something happens to it while you are in the middle of a root canal? Can Forward Enterprise help?
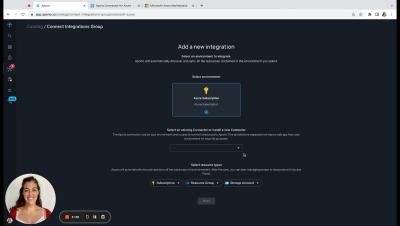
Importing to Egnyte's eTMF
Importing completed trial data into Egnyte’s eTMF allows you to keep your clinical studies inspection ready at all times!
Trust Talks with Aaron Kirkpatrick, CISO at Venminder
Sravish sits down with Aaron Kirkpatrick to discuss the latest security and GRC trends.
Tutorial: Optimize Mobile VPN with SSL Throughput
#cybersecurity #technology #watchguard #wgsupport #firebox #sslvpn
This video covers how to restrict access to local resources for VPN users.
To learn more about WatchGuard Support and other features, follow the link: https://wgrd.tech/3FoQ0eg
How To Discover PII and Privacy Vulnerabilities in Structured Data Sources
In this video, we walk through the process of discovering personally identifiable information (PII) and identifying potential privacy vulnerabilities within structured data sources. First, you will connect Protecto to your data repository. Then, we will show you how to access the Privacy Risk Data within your data assets catalog, obtain information on active users, access privileges, data owners, and recommendations for dealing with privacy risks.
Container Security Fundamentals - Linux Capabilities (Part 1)
In this video we're looking at how Linux capabilities can be used by general programs and containers to provide only specific rights they need instead of providing "root" privileges. To learn more, read our blog on Datadog’s Security Labs site.
Why Life Science Leaders Trust Egnyte
Biotechs need efficiency and speed, so leading firms like Sionna, Digitalis Ventures, Nimbus, and EQRx bet on Egnyte. See how they leverage Egnyte’s simplicity, security, and support to drive collaboration, innovation, and results. From rapid eTMF deployment to seamless teamwork, Egnyte is purpose-built for biotech speed.