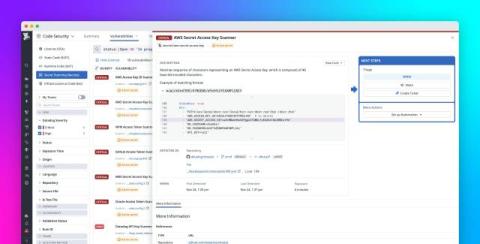
Secure your code at scale with AI-driven vulnerability management
As development teams adopt generative AI at an unprecedented pace, security teams face an evolving set of challenges in securing the software development life cycle. The increasing speed and scale of code changes make it more difficult for organizations to manage risk effectively. Legacy scanners often fail to keep up, returning slow results and noisy alerts that increase remediation time and leave organizations exposed to potential breaches.