Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Incident Response
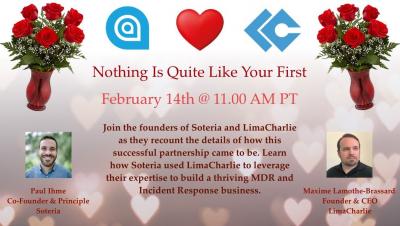
A Cybersecurity Love Story
Tetra Defense Joins Arctic Wolf to Transform Incident Readiness and Response
Kubernetes Incident Response: Building Your Strategy
Kubernetes is the popular container orchestration platform developed by Google to manage large-scale containerized applications. Kubernetes manages microservices applications over a distributed cluster of nodes. It is very resilient and supports scaling, rollback, zero downtime, and self-healing containers. The primary aim of Kubernetes is to mask the complexity of overseeing a large fleet of containers.
CrowdStrike Services Offers Incident Response Tracker for the DFIR Community
During a recent client engagement for a tabletop exercise (TTX), it became apparent that the client did not have a methodology for tracking indicators and building an incident timeline. The CrowdStrike Services team wanted to provide more information to our client on how incidents can and should be tracked, but nothing was available in the public domain.
Building Out SaaS Incident Response Capabilities
Every functioning security team has an incident response plan. Advance strategizing and preparation are absolutely imperative to ensure a quick response to data breaches, ransomware, and numerous other challenges, but most companies first developed that plan years, if not decades, ago and now only revisit it periodically. This is a problem. How many organizations have developed a separate incident response plan to address the unique risks of the software-as-a-service (SaaS) era? Far too few.
Arctic Wolf Cloud Detection and Response
What Is a Cybersecurity Incident Response Plan?
Handling an incident in LimaCharlie: best practices, capabilities, tips & tricks
Elevating What a TIP Can Be - The ThreatQ Platform
In a previous blog I reviewed the foundational use case for a TIP, which is threat intelligence management—the practice of aggregating, analyzing, enriching and de-duplicating internal and external threat data in order to understand threats to your environment and share that data with a range of systems and users. However, one of the unique benefits of the ThreatQ Platform and where organizations are deriving additional business value, is that it also allows you to address other use cases.