Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Zero Trust
What is Zero Standing Privilege (ZSP)?
Zero standing privilege (ZSP) is an applied zero trust security strategy for privileged access management (PAM). The term zero standing privilege was coined by an analyst at Gartner. In practice, it implies no users should be pre-assigned with administrative account privileges. Zero-trust security forbids authorization based on static predefined trust boundaries.
Working with At-Risk Businesses: How It Can Dismantle Your Zero Trust Strategy
Nowadays, building a zero-trust network has become a standard protocol in the era of evolving business models, multiple workforce platforms, cloud adoption, and increased device connectivity. But, if a business continues to work with at-risk organizations, the zero-trust policy crumbles. Working with well-secured third parties that uphold a zero-trust strategy is crucial for optimal cybersecurity within any business.
The Business Value of Security Service Edge (SSE) and the SASE and Zero Trust Journey
I’m not big on acronyms or buzzwords. Like many executives, my eyes glaze over when I’m being prospected with an alphabet soup of technology terms I supposedly “need” to care about. So why, then, does the title of this article include Security Service Edge (SSE), Secure Access Service Edge (SASE), and Zero Trust? Despite our justified disdain for acronyms, the ideas behind these terms hold genuine importance for business leaders.
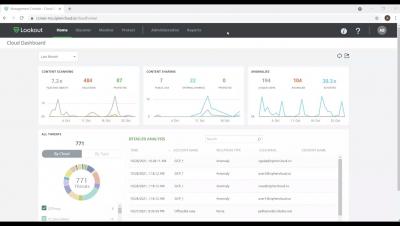
Lookout ZTNA - Intro to onboarding an application, securing access and protecting sensitive data.
Lookout ZTNA - Creating Policies for data protection and application security
Automated Zero Trust: The Only Thing to Put Your Trust in
There’s no question that centralized identity and access management (IAM) helps companies reduce risk and prevent attacks. But, as this week’s Okta attack shows, centralized IAM doesn’t eliminate all risks. Attackers with access to IAM data can use this information to easily access downstream systems or modify permissions to grant elevated access to malicious parties.
We need to bear in mind 5 key lessons when implementing a zero-trust model:
In today's ecosystems, a single enterprise can operate multiple internal networks, remote offices with their own local infrastructure, remote and/or mobile individuals and Cloud services. According to the study published by NIST, this level of complexity is too much for legacy network security models that are based on the location of the company infrastructure and there isn’t a single, easily identifiable perimeter for all elements.
Cloudflare and CrowdStrike Expand Partnership to Bring Integrated Zero Trust Security to Devices, Applications and Networks
CrowdStrike and Cloudflare Expand Zero Trust from Devices and Identities to Applications
Threat actors continue to exploit users, devices and applications, especially as more of them exist outside of the traditional corporate perimeter. With employees consistently working remotely, adversaries are taking advantage of distributed workforces and the poor visibility and control that legacy security tools provide.