Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cyberattacks
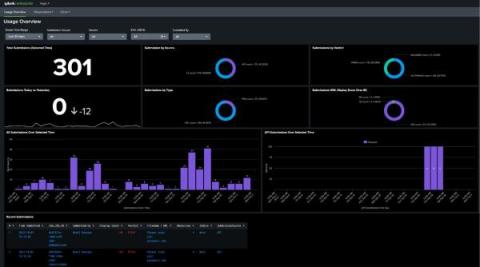
Introducing Splunk Add-On for Splunk Attack Analyzer and Splunk App for Splunk Attack Analyzer
Microsoft 365 targeted by Cybercriminals with LinkedIn Smart Links Cyber Attacks
What Are Microsoft 365 LinkedIn Smart Links? LinkedIn Smart Links are a relatively new feature introduced by LinkedIn to simplify the way users share content, profiles, and documents within the platform. Smart Links allow you to share specific pieces of content, making it easier for connections to access information you deem relevant. Smart Links are dynamic, which means they change each time someone accesses the link.
HTTP/2 Rapid Reset: deconstructing the record-breaking attack
Starting on Aug 25, 2023, we started to notice some unusually big HTTP attacks hitting many of our customers. These attacks were detected and mitigated by our automated DDoS system. It was not long however, before they started to reach record breaking sizes — and eventually peaked just above 201 million requests per second. This was nearly 3x bigger than our previous biggest attack on record.
HTTP/2 Zero-Day Vulnerability Results in Record-Breaking DDoS Attacks
Earlier today, Cloudflare, along with Google and Amazon AWS, disclosed the existence of a novel zero-day vulnerability dubbed the “HTTP/2 Rapid Reset” attack. This attack exploits a weakness in the HTTP/2 protocol to generate enormous, hyper-volumetric Distributed Denial of Service (DDoS) attacks.
74% of CEOs Concerned About Their Organization's Ability to Protect Against Cyber Attacks, Despite Seeing Cybersecurity as Critical
According to the recent The Cyber-Resilient CEO report released by IT services and consulting agency Accenture, a staggering 74% of CEOs have expressed concerns about their organizations' ability to protect their businesses from cyber attacks. This is despite the fact that 96% of CEOs acknowledge the importance of cybersecurity for the growth and stability of their organizations.
Clorox Experiences Significant Financial Loss Stemming From Recent Cyber Attack
American global manufacturer of cleaning products Clorox stated that recent sales and profit loss to a cyber attack. In a statement from Clorox's press release, "As previously disclosed, the Company believes the cybersecurity attack has been contained and the Company is making progress in restoring its systems and operations. The available information does not confirm whether the Clorox cyber attack was a ransomware incident.
How Sysdig can detect Impersonation Attacks in Okta IdP
To combat the growing threat of identity attacks, organizations need to adopt a proactive approach that goes beyond traditional security measures. Identity Threat Detection and Response (ITDR) is one such approach that focuses on monitoring and responding to suspicious activities related to user identities and access management. ITDR solutions can help organizations spot unusual patterns, such as multiple failed login attempts, access from unusual locations, or abnormal behavior within the system.
The role of automation in mitigating cybersecurity risks
Cyberattacks are on the rise around the globe. Recent data suggest that there are 2,200 cyberattacks every day and that the average cost of a data breach is $9.44 million. Of those cyberattacks, 92% are delivered via email in the form of malware and phishing. In 2022 alone, businesses reported 255 million phishing attacks with an average cost of $4.91 million.