- January 2025 (6)
- December 2024 (9)
- November 2024 (14)
- October 2024 (10)
- September 2024 (10)
- August 2024 (12)
- July 2024 (11)
- June 2024 (8)
- May 2024 (15)
- April 2024 (9)
- March 2024 (10)
- February 2024 (17)
- January 2024 (8)
- December 2023 (2)
- November 2023 (3)
- October 2023 (6)
- September 2023 (14)
- August 2023 (7)
- July 2023 (9)
- June 2023 (9)
- May 2023 (9)
- April 2023 (3)
- March 2023 (13)
- February 2023 (9)
- January 2023 (7)
- December 2022 (4)
- November 2022 (17)
- October 2022 (12)
- September 2022 (12)
- August 2022 (7)
- July 2022 (6)
- June 2022 (13)
- May 2022 (11)
- April 2022 (7)
- March 2022 (14)
- February 2022 (5)
- January 2022 (9)
- December 2021 (9)
- November 2021 (5)
- October 2021 (7)
- September 2021 (9)
- August 2021 (4)
- July 2021 (4)
- June 2021 (5)
- May 2021 (6)
- April 2021 (6)
- March 2021 (11)
- February 2021 (6)
- January 2021 (7)
- December 2020 (6)
- November 2020 (8)
- October 2020 (8)
- September 2020 (9)
- August 2020 (2)
- July 2020 (7)
- June 2020 (4)
- May 2020 (7)
- April 2020 (6)
- March 2020 (3)
- February 2020 (3)
- January 2020 (3)
- December 2019 (3)
- November 2019 (11)
- October 2019 (4)
- September 2019 (1)
- August 2019 (3)
- July 2019 (3)
- June 2019 (3)
- May 2019 (7)
- April 2019 (6)
- March 2019 (6)
- February 2019 (4)
- January 2019 (1)
- October 2018 (1)
- May 2018 (1)
- April 2018 (1)
- March 2018 (1)
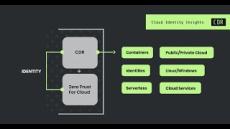
Sysdig is the first unified approach to monitor and secure containers across the entire software lifecycle.
Sysdig was born out of the belief that open source tools will be at the foundation of your next generation infrastructure. See our projects for system visibility, and container security, as well as partner projects we’ve embraced.
Accelerate your transition to containers, and then have confidence in your ongoing operations. We've built the cloud-native intelligence platform to create a single, more effective way to secure, monitor, and assure your critical applications:
- Container security (Sysdig Secure): Protect and assure your applications. Bring together image scanning and run-time protection to identify vulnerabilities, block threats, enforce compliance, and audit activity across your microservices.
- Enterprise-grade Docker monitoring (Sysdig Monitor): Enhance software reliability and accelerate problem resolution with advanced Kubernetes integration and built-in Prometheus monitoring capabilities.
- Automatic orchestrator integration (Sysdig ServiceVision): We use Sysdig ServiceVision to dynamically map services using metadata from Kubernetes, OpenShift, AWS, Azure, Google, Mesos, or Docker EE, and more. With this insight, you can isolate and solve problems faster.
Our container intelligence platform monitors and secures millions of containers across hundreds of enterprises, including Fortune 500 companies and web-scale properties.