Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
4 Ways Veracode Fix Is a Game Changer for DevSecOps
In the fast-paced world of software development, too often security takes a backseat to meeting strict deadlines and delivering new features. Discovering software has accrued substantial security debt that will take months to fix can rip up the schedules of even the best development teams. An AI-powered tool that assists developers in remediating flaws becomes an invaluable asset in this context.
Five Questions Security Teams Need to Ask to Use Generative AI Responsibly
Since announcing Charlotte AI, we’ve engaged with many customers to show how this transformational technology will unlock greater speed and value for security teams and expand their arsenal in the fight against modern adversaries. Customer reception has been overwhelmingly positive as organizations see how Charlotte AI will make their teams faster, more productive and learn new skills, which is critical to beat the adversaries in the emerging generative AI arms race.
Strengthen Your Identity Security: CyberArk's Integration with AWS
Don't Let the Cyber Grinch Ruin your Winter Break: Project Cybersafe Schools protects small school districts in the US
As the last school bell rings before winter break, one thing school districts should keep in mind is that during the winter break, schools can become particularly vulnerable to cyberattacks as the reduced staff presence and extended downtime create an environment conducive to security lapses. Criminal actors make their move when organizations are most vulnerable: on weekends and holiday breaks.
AI and Cybersecurity in 2024 - What's Changing and Why It Matters
Tired of the AI hype? We get it. Our latest blog takes a no-nonsense look at AI in 2024's cybersecurity – just the facts and some thoughtful insights. No earth-shattering revelations, just a decent read for your coffee break.
Top 5 Technology Must-Haves for Financial Services and Banking
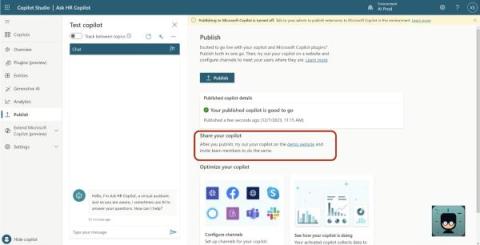
Microsoft Copilot Studio Vulnerabilities: Explained
Cloudflare WAF: Old concept, new threats - Innovations in WAF with Demo
Australia's cybersecurity strategy is here and Cloudflare is all in
We are thrilled about Australia’s strategic direction to build a world-leading cyber nation by 2030. As a world-leading cybersecurity company whose mission is to help build a better Internet, we think we can help. Cloudflare empowers organizations to make their employees, applications and networks faster and more secure everywhere, while reducing complexity and cost.