Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to Make OpenClaw More Secure
OpenClaw is the hottest opensource AI tool, but it comes with massive security risks. In this video I'll give you the controls to mitigate these risks.
Tech Talk | Print, Leak, Repeat: UEBA Insider Threats You Cant Ignore
Insider threats thrive in ambiguity. They exist in the space where everyday work and malicious intent overlap. Traditional defenses are not built to detect that overlap, they are built to stop outsiders, not to question the behavior of insiders who look legitimate until the moment they are not. User Entity and Behavior Analytics (UEBA) fills that gap by establishing a behavioral perimeter around every identity and device.
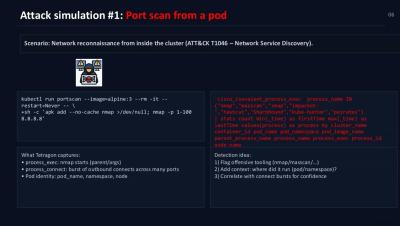
Splunking Isovalent Data: Attack Simulations and Detections
We simulate real-world adversary behaviors inside a Kubernetes cluster to validate how Tetragon’s kernel-level visibility translates into detectable, high-fidelity security signals in Splunk. Each simulation maps to techniques in the MITRE ATT&CK for Containers framework and showcases how eBPF instrumentation allows us to catch what traditional agents often miss—for example, process lineage, syscall context, and Kubernetes workload-level attribution.
Splunk report: Agentic AI takes centre stage in CISOs' path to digital resilience
Nearly all CISOs report they are now responsible for AI governance and risk management, cite the growing sophistication of threat actor capabilities as their greatest risk. Vast majority say AI enables more security events to be reviewed.
Featured Post
The new-age SOC analyst in 2026: tier 1.5
The role of the tier 1 SOC analyst has always been critical. It's the function responsible for holding the line day-to-day and responding when incidents happen. It's also the training ground for analysts, training them in a wide range of basics to prepare them to advance to tier 2. It's a role that has never been static but with the pace of change noticeably faster than ever before, the role of the tier 1 SOC analyst is evolving once again.
How SPL2 Simplifies Security Investigations and Admin Workflows in Splunk
Discover how SPL2 (Splunk Processing Language 2) is transforming the way organizations manage data at scale. In this demo, we dive deep into how SPL2 addresses modern data challenges by offering a unified, SQL-like syntax and powerful new tools like the Module Editor. With syntax that’s instantly familiar to current users, SPL2 removes barriers to adoption and lets teams leverage its power from day one.
When Your Fraud Detection Tool Doubles as a Wellness Check: The Unexpected Intersection of Security and HR
Let’s face it: humans are creatures of habit, and nothing rattles us quite like the prospect of change. (Just ask anyone who’s dared to swap out the office coffee brand—revolutions have started over less.) According to SHRM's research on change fatigue, today’s relentless pace of disruption is exhausting employees faster than a budget ergonomic chair. But here’s where it gets fascinating—where security, HR, and fraud analysis converge in ways you might not expect.
Hashing in Cryptography Explained: How It Works, Algorithms, and Real-World Uses
Hashing takes your data (like a password or file) and converts it into a fixed-length code that can’t be reversed. This makes it nearly impossible for attackers to figure out what the original data was, even if they steal the hash. In this article, I’ll explain hashing in detail, including its working principles, applications, the algorithms behind it, and how to apply it correctly.
Zero-shot Security Classification with Foundation-Sec-8B and Splunk DSDL
Earlier this year, we showcased how the Foundation-Sec-8B model’s chat capabilities can be leveraged within the Splunk App for Data Science and Deep Learning (DSDL) to summarize security events and provide detection suggestions. Building on its robust security expertise, Foundation-Sec-8B also supports zero-shot classification for a wide range of security tasks.