Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cloud Monitoring: Critical for Business Success
From automated compliance to AI: How investors are prioritizing security
AI and cybersecurity are top strategic priorities for companies at every scale — from the teams using the tools to increase efficiency all the way up to board leaders who are investing in AI capabilities.
What To Look For in an Open Source Vulnerability Scanner
One of the top security concerns we hear from technology leaders is about the security of open source software (OSS) and cloud software development. An open source vulnerability scanner (for scanning OSS) helps you discover risk in the third-party code you use. However, just because a solution scans open source does not mean you are ultimately reducing security risk with it.
Privacy Pass: Upgrading to the latest protocol version
The challenge of telling humans and bots apart is almost as old as the web itself. From online ticket vendors to dating apps, to ecommerce and finance — there are many legitimate reasons why you'd want to know if it's a person or a machine knocking on the front door of your website. Unfortunately, the tools for the web have traditionally been clunky and sometimes involved a bad user experience.
The Darkside of GraphQL
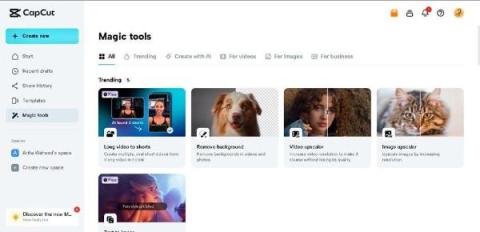
Unleashing Creativity: Exploring CapCut's Online Photo Editor for Dynamic Graphic Design
Addressing the Rising Threat of API Leaks
In the realm of cybersecurity, the metaphor of "Leaky Buckets" has become an increasingly prevalent concern, particularly in the context of API security. This term encapsulates the hidden vulnerabilities and exposures in API infrastructures that many organizations struggle to identify and address. The digital era has amplified these challenges, with APIs becoming central to the operational fabric of numerous enterprises.
Mastering IoT Remote Access: Top Strategies for Secure and Efficient Connectivity
Using Veracode Fix to Remediate an SQL Injection Flaw
In this first in a series of articles looking at how to remediate common flaws using Veracode Fix – Veracode’s AI security remediation assistant, we will look at finding and fixing one of the most common and persistent flaw types – an SQL injection attack. An SQL injection attack is a malicious exploit where an attacker injects unauthorized SQL code into input fields of a web application, aiming to manipulate the application's database.