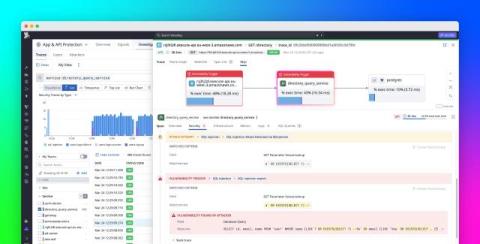
Detect runtime threats in Python Lambda functions with Datadog AAP
Python AWS Lambda functions are ephemeral and highly distributed, which creates security visibility gaps that traditional perimeter defenses and proxy-based controls struggle to fill. Techniques such as credential stuffing, SQL injection, and server-side request forgery (SSRF) can look like legitimate application traffic, making them difficult to identify without visibility inside the application itself.