XDR meets AIOps for Faster AI-Driven Detection and Resolution
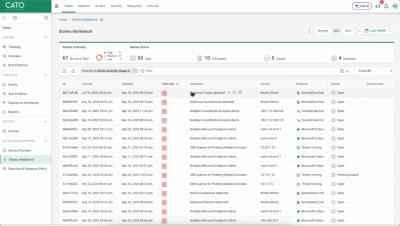
Discover how Cato Networks helps you respond to security and networking issues quickly, easily and efficiently, in one place, with the AI power of Cato XOps. Watch this demo to see how XOps brings together XDR and AIOps to cut through huge volumes of events and alerts and provide one place to see what’s important, to investigate issues, and to mitigate threats quickly - across networking and security.