When Trust Becomes a Liability: The Salesloft Drift Breach and the Hidden Risk of SaaS Integrations
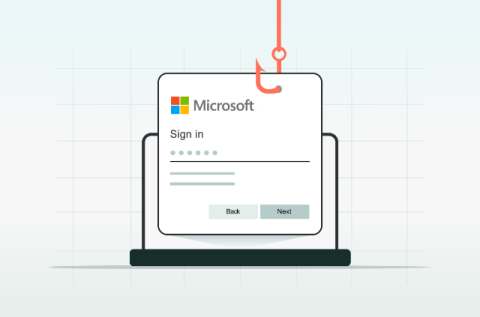
This was not a brute-force intrusion, the attackers persuaded or tricked systems into granting long-lived access, then quietly exploited that trust.