Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
October 2023
7 Types of Social Engineering Attacks
DDoS Traffic Analysis Techniques for SOC Teams
SQL server attacks: mechanisms you must know
DDoS threat report for 2023 Q3
Welcome to the third DDoS threat report of 2023. DDoS attacks, or distributed denial-of-service attacks, are a type of cyber attack that aims to disrupt websites (and other types of Internet properties) to make them unavailable for legitimate users by overwhelming them with more traffic than they can handle — similar to a driver stuck in a traffic jam on the way to the grocery store.
Top Asian/APAC Cybersecurity Threats of 2023
Security in the Property Industry: Challenges and How to Avoid Attacks
In recent years, there has been a major ongoing trend toward more digital infrastructure and an increased dependence on technology across a wide variety of sectors. In the property industry, this has manifested heavily in the growth of the property technology (PropTech) market. These developments have had a serious impact on the sector, enabling advances that both improve existing processes and add new features to real estate transactions.
Block the attack paths into your Kubernetes clusters
Oh-Auth - Abusing OAuth to take over millions of accounts
Piecing Together the Attack on Okta's Support Unit
The October 2023 Okta breach is the latest example in a long line of third-party identity attacks. Based on reports to date, it seems that the attack on Okta’s support case management system enabled a threat actor to launch downstream attacks into other companies. So far, 1Password, BeyondTrust and Cloudflare have publicly confirmed they were targeted. Such attacks don’t discriminate and pointing fingers is unproductive.
What You Need to Know About the October OKTA Breach
What Is an Exploit Kit?
An exploit kit is a toolkit that cybercriminals use to attack the security vulnerabilities of a system or device to distribute malware. An exploit is a bit of code that takes advantage of security vulnerabilities found within software and hardware. Cybercriminals collect these bits of code and compile them into a kit that can target multiple security vulnerabilities at once, and secretly install malware on devices.
Mastering Cybersecurity Challenges: How Crisis Simulations Empower Organizations to Defend Against Cyber Threats
Cyberattacks are a constant and evolving threat across all sectors with 2023 seeing a resurgence in data breaches and ransomware attacks with popular variants like Clop, LockBit, and ALPHV, among others, terrorizing businesses and exploiting system vulnerabilities. The 2021–2022 financial year saw an increase in cybercrime, with over 76,000 reports made to the Australian Cyber Security Centre (ACSC), with no signs of slowing down.
GitHub Copilot code security: XSS in React
In an evolving era of Artificial Intelligence (AI) and Large Language Models (LLMs), innovative tools like GitHub's Copilot are transforming the landscape of software development. In a prior article, I published about the implications of this transformation and how it extends to both the convenience offered by these intelligently automated tools and the new set of challenges it brings to maintaining robust security in our coding practices.
Proactively Preventing Your Company from Becoming the Next Cyberattack Headline
CTI Roundup: Smart Links Attacks Target Microsoft Accounts
Threat actors attempt moving laterally from SQL server to the cloud, ShellBot avoids detection in attacks on Linux SSH servers, and Smart Links attacks target Microsoft accounts.
The Crucial Link
In today’s digital age, businesses rely heavily on technology to drive their operations efficiently and effectively. This dependence on technology has brought about new challenges and risks, particularly in the realm of cybersecurity. As organisations strive to ensure operational resilience, they must recognize the integral role of cyber resilience in safeguarding their digital assets and operations. Cyber threats have become a persistent concern for businesses of all sizes.
How to protect Node.js apps from CSRF attacks
A cross-site request forgery attack (CSRF) attack is a security vulnerability capitalizing on trust between a web browser and a legitimate website. Crafty attackers manipulate browsers into executing malicious actions on websites where users authenticate themselves and log in. Often, these attacks start when users click a link attached to a deceptive email or land on a compromised website, unaware of the logic executing in the background.
HTTP/2 Rapid Reset Attack Vulnerability
Cyberattacks on Gaming Developers: Five Security Tips
Gaming companies collect data concerning user behavior for a variety of reasons: to inform investment and content decisions, enable game and advertisement personalization, and improve gameplay, to name a few. However, the data available provides a daunting task for those attempting to make use of it, as well as a ripe target for attackers. Effectively utilizing and protecting this data can be a challenge, especially as the volume of gaming data increases over time.
What is Threat Exposure Management?
Staying ahead of cyberattacks and strengthening your organization’s defenses doesn’t happen overnight and can be hard to accomplish without the right tools and cyber strategies. SecurityScorecard’s Threat Intelligence team hosted a webinar that highlights the importance of threat exposure management, its latest trends, and how to implement this framework into an organization’s cybersecurity plan.
How To Detect Man-in-the-Middle Attacks
It is notoriously difficult to detect a man-in-the-middle attack. However, these attacks do have some subtle signs, including landing on obviously fake websites and your internet connection mysteriously becoming unreliable. Additionally, man-in-the-middle attacks often happen on open, unencrypted public networks, so it’s very important to be aware of your online environment at all times.
Windows Gaming Host, Shadow PC, Attacked via Malicious Software
Shadow PC is a Paris-based gaming host with thousands of clients in Europe and the US. Shadow’s service allows video games with high resource consumption to run on old software; this is made possible by Shadow’s ability to open a virtual computer. The virtual computer takes the onus of running games, allowing even incompatible computers to run game software. Shadow PC’s services are cloud-based, which should allow up to 100,000 users to play on their servers simultaneously.
Challenge of Cybersecurity Insurance Amid Ransomware Attacks
How a Database Risk Assessment Reduces the Risk of a Cyberattack
Database security often, and to an organization's detriment, falls between the cracks as security and IT teams scramble to stay on top of daily cyber hygiene tasks and deal with the never-ending problems of running their network. The danger of overlooking their database, or to put it in, say, banking terms – the vault – is this is likely a threat actor's primary target. An organization's database is where IP, credentials, and financial information are stored.
DDoS Attacks in 2024: Distributed DoS Explained
HTTP/2 Rapid Reset
A recent vulnerability tracked as Rapid Reset (CVE-2023-44487) in the HTTP/2 protocol was recently disclosed by researchers and vendors. It was exploited in the wild from August 2023 to October 2023. The issue arises from the HTTP/2 protocol's ability to cancel streams using an RST_STREAM frame, which can be misused to overload servers by initiating and quickly canceling numerous streams, circumventing the server's concurrent stream limit.
53% of Organizations Experienced Cyber Attacks
As increasing percentages of businesses experience cyberattacks, new data provides details on where the most organizational risk lies. According to U.K. cyber insurer Hiscox’s Cyber Readiness Report 2023, attacks are on the rise: With these increases, how prepared are organizations? According to Hiscox, organizations are spending money on the problem; the median cybersecurity spend is a little over $1.39 million (with enterprises spending $4.9 million).
New Cyber Attack Techniques Will Not Replace Old-School Social Engineering
Even though there are new attack types for cybercriminals, they are still leveraging old-school attack vectors. Why? Because they still work. I cover new attack methods all the time, with recent examples including a sophisticated phishing campaign impersonating Microsoft and an attack last month targeting the Ukrainian military.
Cyber Attack on Merck | Cyber Insurance
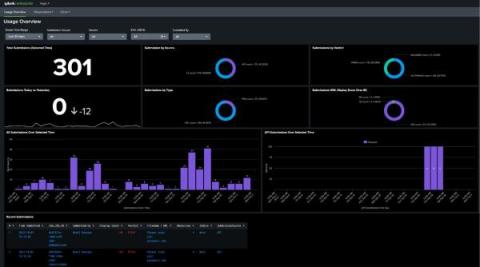
Introducing Splunk Add-On for Splunk Attack Analyzer and Splunk App for Splunk Attack Analyzer
Microsoft 365 targeted by Cybercriminals with LinkedIn Smart Links Cyber Attacks
What Are Microsoft 365 LinkedIn Smart Links? LinkedIn Smart Links are a relatively new feature introduced by LinkedIn to simplify the way users share content, profiles, and documents within the platform. Smart Links allow you to share specific pieces of content, making it easier for connections to access information you deem relevant. Smart Links are dynamic, which means they change each time someone accesses the link.
74% of CEOs Concerned About Their Organization's Ability to Protect Against Cyber Attacks, Despite Seeing Cybersecurity as Critical
According to the recent The Cyber-Resilient CEO report released by IT services and consulting agency Accenture, a staggering 74% of CEOs have expressed concerns about their organizations' ability to protect their businesses from cyber attacks. This is despite the fact that 96% of CEOs acknowledge the importance of cybersecurity for the growth and stability of their organizations.
HTTP/2 Rapid Reset: deconstructing the record-breaking attack
Starting on Aug 25, 2023, we started to notice some unusually big HTTP attacks hitting many of our customers. These attacks were detected and mitigated by our automated DDoS system. It was not long however, before they started to reach record breaking sizes — and eventually peaked just above 201 million requests per second. This was nearly 3x bigger than our previous biggest attack on record.
HTTP/2 Zero-Day Vulnerability Results in Record-Breaking DDoS Attacks
Earlier today, Cloudflare, along with Google and Amazon AWS, disclosed the existence of a novel zero-day vulnerability dubbed the “HTTP/2 Rapid Reset” attack. This attack exploits a weakness in the HTTP/2 protocol to generate enormous, hyper-volumetric Distributed Denial of Service (DDoS) attacks.
Clorox Experiences Significant Financial Loss Stemming From Recent Cyber Attack
American global manufacturer of cleaning products Clorox stated that recent sales and profit loss to a cyber attack. In a statement from Clorox's press release, "As previously disclosed, the Company believes the cybersecurity attack has been contained and the Company is making progress in restoring its systems and operations. The available information does not confirm whether the Clorox cyber attack was a ransomware incident.
How Sysdig can detect Impersonation Attacks in Okta IdP
To combat the growing threat of identity attacks, organizations need to adopt a proactive approach that goes beyond traditional security measures. Identity Threat Detection and Response (ITDR) is one such approach that focuses on monitoring and responding to suspicious activities related to user identities and access management. ITDR solutions can help organizations spot unusual patterns, such as multiple failed login attempts, access from unusual locations, or abnormal behavior within the system.
The role of automation in mitigating cybersecurity risks
Cyberattacks are on the rise around the globe. Recent data suggest that there are 2,200 cyberattacks every day and that the average cost of a data breach is $9.44 million. Of those cyberattacks, 92% are delivered via email in the form of malware and phishing. In 2022 alone, businesses reported 255 million phishing attacks with an average cost of $4.91 million.
The Evolution of Security and Identity is Key to Successful Digital Transformation
The Evolution of Security and Identity is Key to Successful Digital Transformation. Not a day goes by when we don’t hear about yet another data breach or sophisticated compromise. As a result, there cannot be a C-Suite executive that is unaware of the cyber threats their organisation faces, either through guidance from their security teams or the constant media reporting of ransomware or data theft as a result of successful cyber-attacks.
What Is a Watering Hole Attack?
A watering hole attack is a type of cyberattack in which a threat actor targets an organization by hacking a website often visited by an employee in order to infect the employee’s device with malware. Once the device of one employee is infected, the threat actor targets other members of the organization and steals their confidential information.