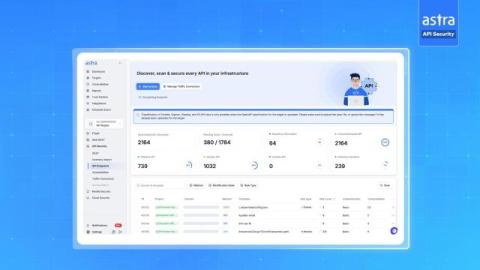
Business logic: The silent future of cyberattacks
Future hacks won’t trigger alarms or leave traces. No security measures will be violated. The systems are functioning normally – but the loss is real. As automated defenses improve, attackers must target what machines can’t: the business processes. By exploiting flaws in workflow logic, hackers can steal data and funds in a way no one expected. Business logic vulnerabilities are now a serious cybersecurity blind spot, and a leading method for breaching even the most secure systems.