Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Data Breaches
College's data leak posing a significant security risk in southern Indian region
A thriving hacker has been found to be posting a college database showcasing it to be a breach. This happened to one of the colleges in the southern region of India, Kerala. Necessary measures have been taken to keep them up to date! The college’s information was found to be floating around on the Dark Web. These data seem to be highly sensitive. These data could be acquired by any human being for just a few thousand.
The Latest Cybersecurity Threats Facing Businesses
It's incredibly important that you learn the latest cybersecurity threats that can threaten a business in 2023. Learn them here.
What is a data breach?
A fatal retweet: How the newest attack on Twitter can teach us a lesson on cybersecurity
In what may be the largest Twitter data breach attack to date, the personal data of over 400 million users was stolen from the social media giant’s grasp and put up for sale on the dark net on the day after Christmas. This attack couldn’t have happened at a worse time for the company, as the Irish Data Protection Commission (DPC) has announced an investigation into an earlier Twitter data leak in November 2022 that had affected over 5.4 million users.
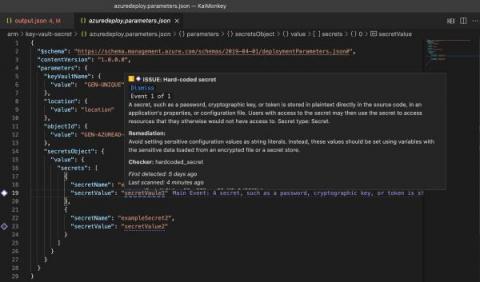
Supply chain security incident at CircleCI: Rotate your secrets
On January 4, CircleCI, an automated CI/CD pipeline setup tool, reported a security incident in their product by sharing an advisory.
CircleCI Breach: How to Rotate All Stored Secrets ASAP
Breach Bulletin: The most important data breaches from December 2022
It’s rare that a week goes by without at least one data breach making the news. Criminals are targeting companies of all sizes to see if they can slip past their digital defenses and steal confidential data.
A Hacker Claims to Have Obtained Data of 400M Twitter Users
Read also: ByteDance caught using TikTok to spy on reporters, BitKeep users lost $8 million in assets in a hack, and more.
Latest LastPass security breach highlights developers as a high-value target
Last August, the maintainers of the LastPass cloud-based password manager tool reported a security breach in their servers. The disclosure maintained that an unauthorized party gained access to the LastPass development environment through a single compromised developer account. However – while source code and technical information was stolen, no user data was compromised and no services were interrupted. This specific statement about user data was reiterated many times.