Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cyberattacks
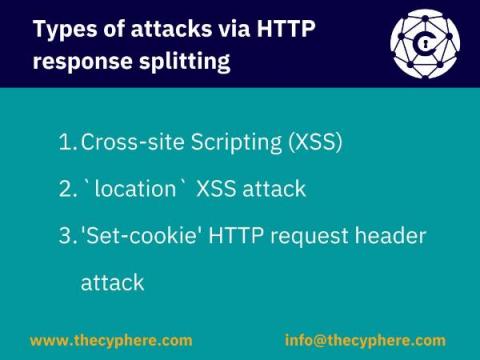
HTTP Response Splitting Attack
HTTP Response Splitting entails a kind of attack in which an attacker can fiddle with response headers that will be interpreted by the client. The attack is simple: an attacker passes malicious data to a vulnerable application, and the application includes the malicious data in the single HTTP response, thus leading a way to set arbitrary headers and embedding data according to the whims and wishes of the attacker.
Australia and the Risk of a Russian Cyber Attack: Are You Ready?
Given Russia's reputation for highly-sophisticated cyberattacks, the country's invasion of Ukraine has sparked justified fears of an imminent global cyberwar. While, for the time being, Putin’s cyber efforts against Ukraine are surprisingly restrained, this may not be the case for other countries.
EPP/EDR: What Is It and How Can It Help to Keep Your Organization Safe?
Endpoint devices played a big part in malware and ransomware attacks in 2021. According to a study covered by Help Net Security, security researchers detected more malware and ransomware endpoint infections in the first nine months of the year than they did for all of 2020. Attack scripts leveraging PowerSploit, Cobalt Strike, and other tools were particularly prevalent in that nine-month period, having grown 10% over the previous year after having already climbed 666% compared to 2019.
Russia-Ukraine Crisis Heightens Malicious Cyber Activity: 8 Ways to Bolster Your Cyber Defense
The ongoing war between Ukraine and Russia has placed organizations worldwide on full alert due to the possibility that cyber attacks related to the conflict may impact organizations outside the region.
How to Prevent Whaling Attacks: A Complete Guide
Senior-level executives handle sensitive data and information daily – making them an enticing target for cybercriminals. One of the most complex schemes to date is the whaling attack, in which hackers impersonate high-ranking employees to gain access to computer systems and networks. Whaling attacks have seen a dramatic 131% increase between Q1 2020 and Q1 2021, costing enterprises around $1.8 billion in damages.
What Are Attack Surfaces and How to Protect Them
Research reveals the extent of hackers using default credentials to target businesses
Stevenage, 15th March 2022 – Today new findings from the Bulletproof Annual Cyber Security Industry Threat report highlight the issue posed by poor security hygiene as automated attacks remain a high security threat to businesses. The research gathered throughout 2021, showed that 70% of total web activity is currently bot traffic.
Attackers vs Defenders: Mind the Perspective Gap
Rapid proliferation of data, growing volume of domains and subdomains, and rise in third-party software have expedited the need for having a robust security program in place. As the web-facing attack surface grows, existing security practices are falling behind.