Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How Corelight Uses AI to Empower SOC Teams
The explosion of interest in artificial intelligence (AI) and specifically large language models (LLMs) has recently taken the world by storm. The duality of the power and risks that this technology holds is especially pertinent to cybersecurity. On one hand the capabilities of LLMs for summarization, synthesis, and creation (or co-creation) of language and content is mind-blowing.
CVE-2023-3595: Rockwell Automation ControlLogix Vulnerability Analysis Fuels Better Risk Assessment and Threat Detection
Detecting account compromise with UEBA detection packages
Google introduces real-time scanning on Android devices to fight malicious apps
It doesn't matter if you have a smartphone, a tablet, a laptop, or a desktop computer. Whatever your computing device of choice, you don't want it impacted by malware. And although many of us are familiar with the concept of protecting our PCs and laptops with security software that aims to identify attacks in real-time, it's not a defence that is as widely adopted on mobile devices.
Exploring the Cybersecurity Landscape: Insights from Shira Rubinoff and Gideon Hazam
The Art of Team Building: Blueprints from the Black Hat NOC
It has been a distinct honor to be a part of the Corelight team that helped defend this year’s Black Hat events. I started the event season in the Network Operations Center (NOC) at Black Hat Asia, and then capped it off at Black Hat in Las Vegas. In this blog I’ll share my experience and learnings from participating in both NOCs.
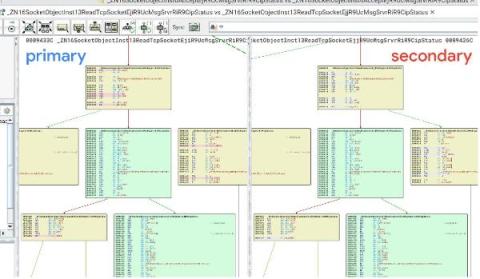
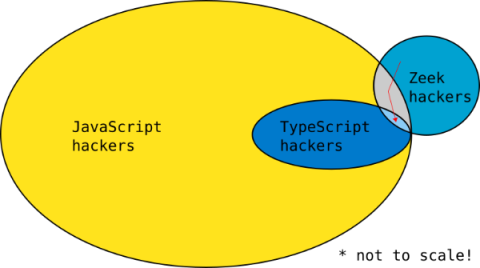
Writing a Zeek package in TypeScript with ZeekJS
Zeek® is the world’s most widely used network security monitoring platform and is the foundation for Corelight network evidence. In this blog I share how to write a Zeek package in TypeScript with a new capability called ZeekJS that was released as part of Zeek 6.0.
Most Organizations Believe Malicious Use of AI is Close to Evading Detection
As organizations continue to believe the malicious use of artificial intelligence (AI) will outpace its defensive use, new data focused on the future of AI in cyber attacks and defenses should leave you very worried. It all started with the proposed misuse of ChatGPT to write better emails and has (currently) evolved into purpose-built generative AI tools to build malicious emails. Or worse, to create anything an attacker would need using a simple prompt.