Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Top 15 Kubectl plugins for security engineers
Let's dig deeper into this list of Kubectl plugins that we strongly feel will be very useful for anyone, especially security engineers. Kubernetes, by design, is incredibly customizable. Kubernetes supports custom configurations for specific use case scenarios. This eliminates the need to apply patches to underlying features. Plugins are the means to extend Kubernetes features and deliver out-of-the-box offerings.
Utilizing Tines' Automation Capability Matrix
Automation is often seen as the natural progression for a security operations center. However, deciding where and when to implement it can be pretty challenging. As an earlier blog post covers, Tines' Automation Capability Matrix is an innovative set of techniques that empower security operations teams to respond proactively and tackle common cyber-security incidents.
Ransomware in the Construction Industry: How Unregulated Data Makes it a Soft Target | John Goecke
Any2Cloud to Recover Kubernetes Clusters from GKE to AKS
The 443 Episode 225 - The RCE Vulnerability That Wasn't
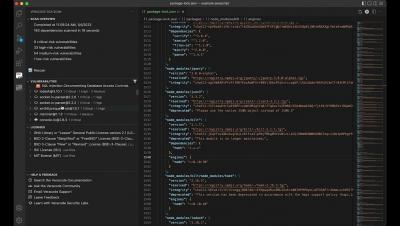
Veracode SCA Scan for VS Code Plugin
Switching Between Multiple Domains
Does Your Organization Meet the 9 Core Capabilities Essential for Zero Trust in IoT?
Every one of your IoT devices has their own machine identity. But how are these identities the key to achieving Zero Trust IoT project? Today’s PKI (Public Key Infrastructure) vendors have specific solutions for managing non-human identities – machines – like servers, laptops, software applications, API’s and other assets found within a corporate network.
Ransomware Recovery: RTO and Optimizing the Recovery Process
Recovery Time Objectives (RTOs) are on everyone’s mind. It bears repeating, one of the most fundamental ways to reduce recovery time from a ransomware or cybersecurity attack is being well prepared and ready to take actions quickly and effectively. This is one of the many variables firmly within a customer’s control and key to a faster and more efficient recovery process. A ransomware attack can be one of the most stressful events an organization and its employees will encounter.