Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How Arctic Wolf Stops Business Email Compromise
In this demo, follow along as we investigate an alert leading to suspicious events that uncover a full business email compromise (BEC attack).
Prompt Injection: New Attack Vector for AI Systems | Wallarm Report #Cybersecurity #AIsecurity
You don't need direct access to an AI model to manipulate it. Third-party content like resumes or metadata can inject malicious prompts.
A Guide to Perimeter Defense in Modern Networks
Organizations can’t run without digital systems and connected technologies in today’s fast-moving world. This digital adoption opens new doors for cyber threats as well. Hackers are becoming more advanced and finding new ways to attack organizations’ IT systems to steal sensitive data, disrupt their operations, and harm brand credibility.
Understanding SBOM Standards: A Look at CycloneDX, SPDX, and SWID
Modern applications are no longer giant monoliths, they are a collection of micro services, open-source components, and third-party tools. But this makes it very difficult to actually understand the insides of our applications, particularly when you consider that our open-source dependencies also have open-source dependencies! The Software Bill of Materials (SBOM) plays a key role here. SBOMs provide a detailed inventory of all software components.
Pen Test Results Dropping? Here's Why (And How to Fix It!) #cybersecurity #bountyprograms
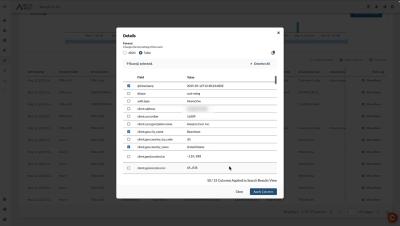
Mend.io, formerly known as Whitesource, has over a decade of experience helping global organizations build world-class AppSec programs that reduce risk and accelerate development -– using tools built into the technologies that software and security teams already love. Our automated technology protects organizations from supply chain and malicious package attacks, vulnerabilities in open source and custom code, and open-source license risks.
Securing AI and Infrastructure with Teleport + Anthropic's Model Context Protocol (MCP)
Securing AI and Infrastructure with Teleport + Anthropic’s Model Context Protocol (MCP) Speakers: As Large Language Models (LLMs) become everyday tools for developers and knowledge workers, ensuring secure, controlled, and auditable access to infrastructure and data is more critical than ever. Join us to learn how Teleport is integrating with Anthropic’s Model Context Protocol (MCP) to deliver robust zero-trust security for AI workflows.
What is Vibe Coding? The Pros, Cons, and Controversies
Vibe coding is an approach to AI coding where artificial intelligence generates executable code from natural language prompts, which is then reviewed and refined by human developers to ensure accuracy and security.
Secure your Slack environment with Sumo Logic Cloud SIEM
Slack has become integral for many organizations, powering everything from internal to external communication and project workflows. But as adoption grows, so does risk. Hackers are increasingly targeting Slack as it often contains intellectual property, credentials, and valuable reconnaissance information. Sumo Logic Cloud SIEM now secures your Slack usage against insider and third-party threats by monitoring audit logs for suspicious activity to keep your company and its data protected.