Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
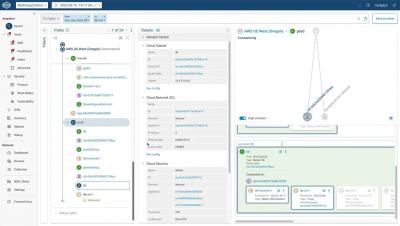
Forward Cloud | Demo
User Office Hours: Exploring Snyk Container
Software Supply Chain Security: The Basics and Four Critical Best Practices
Enterprise software projects increasingly depend on third-party and open source components. These components are created and maintained by individuals who are not employed by the organization developing the primary software, and who do not necessarily use the same security policies as the organization. This poses a security risk, because differences or inconsistencies between these policies can create overlooked areas of vulnerability that attackers seek to exploit.
SLACIP: How to Comply with the SOCI ACT Reforms
On March 31, 2022, the Security Legislation Amendment Critical Infrastructure Protection Act 2022, also known as SLACIP, was passed by the Australian Parliament. The SLACIP Act aims to build upon the SOCI Act framework to improve the security of Australia’s critical infrastructures. To learn how the SOCI Act reforms will affect you and for guidance on how to comply with its new risk management requirements, read on.
Demo: WatchGuard Automation Core API Framework
SOC 2 Type 1 vs. Type 2
Ransomware Attacks Vs. Data Breaches: What's the Difference?
Ransomware attacks and data breaches seem to be continuously contending for the top positions in news feeds. But what's the difference between these cyber threats and which should you be most concerned about? For a comprehensive breakdown of each type of cyberattack, read on.
What is tokenization, what are the types of tokenization, and what are its benefits for eCommerce businesses?
Image source: Freepik This blog was written by an independent guest blogger. As eCommerce grows, there are more issues concerning payments and security. Customers still don’t enjoy a smooth user experience, can’t access fraud-free transactions, and there are still many declined transactions. Online shopping still lacks a seamless experience due to the risks of storing and handling sensitive account data.
Build your robust data strategy the right way
To uncover how to build the best data strategy for your business, we chat with Adam Ryan, Calligo’s Chief Data Officer for Data Strategy on what to do, what to avoid – and everything else in between…