Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
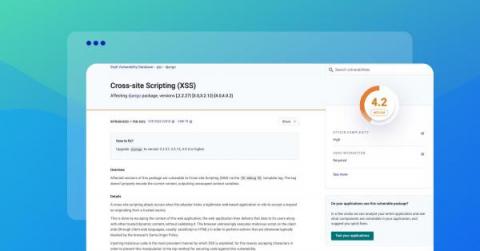
Preventing XSS in Django
Cross-Site Scripting (XSS) is a type of vulnerability that involves manipulating user interaction with a web application to compromise a user's browser environment. These vulnerabilities can affect many web apps, including those built with modern frameworks such as Django. Since XSS attacks are so prevalent, it's essential to safeguard your applications against them. This guide discusses how XSS vulnerabilities originate in Django apps and what you can do to mitigate them.
A Developer's Checklist To Curate Secure Software
Developing software requires immense focus on functionality and especially on its security. According to Intrusion Inc. cost of cybercrimes is increasing at a rapid speed and will cost around USD 10 Trillion. In addition, HackerOne has also issued a report, defining an increase of 65,000 vulnerabilities in different applications and development platforms. In addition, 50% of hackers don’t even report the vulnerability and take advantage for an extended period or until you patch it.
Over 9 Million AT&T Customers Exposed in Recent Cyber Attack
AT&T is a massive telecommunications company with its headquarters in Dallas, Texas. The company is known as the largest telecommunications company in the world according to its revenue, and it is the third-largest mobile phone service provider in the United States. The company recently suffered an attack that exposed some of its customer data to hackers and may have put customers at risk. The attack wasn't on AT&T directly but on one of the company's external marketing vendors instead.
Insights from an external incident response team: Strategies to reduce the impact of cybersecurity attacks
"Why are you here if you cannot decrypt our data?" This is how people sometimes react to the arrival of the external incident response team. In this article, I will try to answer this question, but at the same time, I am going to describe the stages of incident response, list the main mistakes that play into the hands of hackers, and give basic advice on how to respond.
We're changing how we discover and prioritize improvements
For 17 years, we’ve prided ourselves on making 1Password a delight to use. But no product is perfect, and when I hear of someone getting stuck, I get curious. How can we fix it? How can we prevent that friction for future customers?
What's new in Tines: March edition
You can now configure monitoring for your entire Story. And still customize individual Action monitoring right from the Story panel. Get started by configuring Story-level monitoring in your tenant!
How Can GRC Teams Leverage Cyber Risk Quantification?
9 Ways to Jump-Start a Data Privacy Program
With new data privacy regulations going into effect across the globe, small and medium-sized businesses struggle with addressing them effectively. This blog recaps nine key components you should include in your organization’s data privacy program.
ISO27001 Updates: Change is afoot
If you blinked, you might have missed it… On October 25th 2022, the new standard for the Information Security Management System, ISO27001 was released. Without fuss, and without fanfare. But, to quote a famous movie, “There was a great disturbance in the force.” ISO27001 is possibly one of the world's best-known standards for Information Security Management because it has broken out of the realms of the cybersecurity industry and into the world of business.