Weekly Cybersecurity Recap March 10
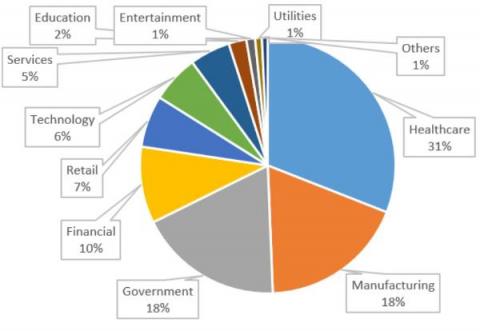
It's been a rough week for major companies and the government as well, with the week finishing off with Washington D.C. lawmakers having their health information exposed. This week's attacks make it very clear that nobody is safe from cyber gangs and hackers. Dole, Dish Network, and Acer all suffered data losses this week, as well as the Crystal Bay Casino.