Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Top 5 Access Control Challenges
Identity and access management (IAM) is an integral part of security systems. Without proper authentication and authorization, it would be impossible to practice cybersecurity principles such as zero trust and least privilege. By now, most organizations have a firm grasp on the identity part of IAM, including concepts like multi-factor and token-based authentication.
Remote Development with Visual Studio Code and Teleport
SELinux, Dragons and Other Scary Things
If you've ever used Linux, you’ve probably heard about SELinux or Security-enhanced Linux. For a very long time, my interaction with it was just restricted to: Like many other security solutions, SELinux can sometimes be annoying, and understanding even the basic concepts can change our bigger enemy to our best friend.
GitGuardian Playbooks Overview
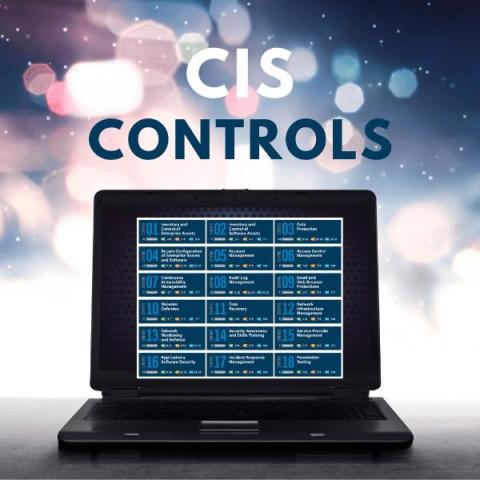
What are CIS Benchmarks and how to use them?
Bootstrapping Terraform Secrets with 1Password CLI
In Modern AppSec, DevSecOps Demands Cultural Change
This is the final of a six-part blog series that highlights findings from a new Mend white paper, Five Principles of Modern Application Security Programs. When thinking of adjectives to describe cyberattackers, it’s doubtful that many people would choose to call them innovative – a term we’re more likely to ascribe to things we enjoy. But the reality is that adversaries are innovative, constantly finding new ways to launch attacks that result in greater rewards for less effort.