Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Practical IT Security Guide to Protecting your People
There is that song by Baz Luhrmann, well it was actually a speech of his first that was later made it into a catchy jingle. It goes … If I could offer you only one tip for the future, sunscreen would be it A long-term benefits of sunscreen have been proved by scientists Whereas the rest of my advice has no basis more reliable Than my own meandering experience, I will dispense this advice now Unfortunately in securing your business, there is no Sunscreen type solution.
What is Post-Quantum Cryptography?
As the technology advances and more business processes become digitalized each day, we seek new ways to protect our valuable data from prying eyes and cyber criminals. Post-quantum cryptography is one of these new ways. In this article, we will discuss what post-quantum cryptography is and why we will need it very soon.
Why cybersecurity needs a seat at the table
A shift has occurred in the bastion of corporate hierarchy in the last few decades that has fundamentally changed how organizations operate. This shift started about sixteen years ago in 1994 with Citibank/Citigroup. After suffering a cybersecurity incident, they created the role of Chief Information Security Officer (CISO); a role which has only grown in prominence since.
Copy and Paste Code: How to Lose Your Job Using Open Source Code
Have you ever wondered whether it’s ok to copy and paste code from an open source project? If you have, you’re not alone. A quick look around several developer websites shows a number of variations on this age-old question. It is never ok to copy and paste code from an open source project directly into your proprietary code. Don’t do it. Just don’t. Even if you’re on a tight deadline. Even if it’s only one loop.
Hardening Windows security: How to secure your organization-Part 3
This is the final blog of our three-part blog series on living-off-the-land (LOTL) attacks. If you missed last week’s blog, you can read it here. LOTL attacks are also known as “malware-free” attacks because your own tools are used against you, either to hide malicious activities under a legitimate system process, or to leverage genuine system activities for malicious purposes.
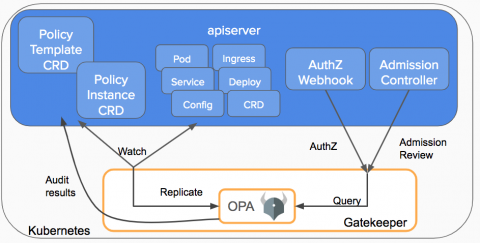
How to monitor OPA Gatekeeper with Prometheus metrics
In this blog post, we’re going to explain how to monitor Open Policy Agent (OPA) Gatekeeper with Prometheus metrics. If you have deployed OPA Gatekeeper, monitoring this admission controller is as relevant as monitoring the rest of the Kubernetes control plane components, like APIserver, kubelet or controller-manager. If something breaks here, Kubernetes won’t deploy new pods in your cluster; and if it’s slow, your cluster scale performance will degrade.
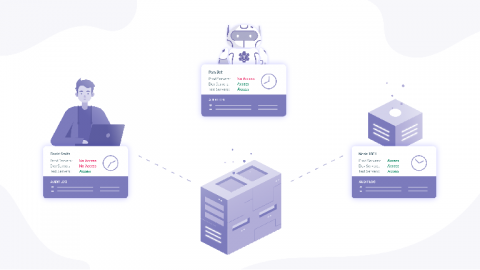
From Zero to Zero Trust
Blockchain, IOT, Neural Networks, Edge Computing, Zero Trust. I played buzzword bingo at RSA 2020, where the phrase dominated the entire venue. Zero Trust is a conceptual framework for cybersecurity that characterizes the principles required to protect modern organizations with distributed infrastructure, remote workforces, and web connected applications.
NormShield vs. SecurityScorecard Comparison
The average cost of a data breach is now nearly $4 million, and the unfortunate truth is third-parties are a significant source of cyber risk. These increasing costs are why cybersecurity vendor risk management (VRM) is a top priority for CISOs, Vice Presidents of Security, and other members of senior management, even at the Board level. In addition to financial costs, regulatory and reputational costs are increasing.
Maze Ransomware - What You Need to Know
Maze is a particularly sophisticated strain of Windows ransomware that has hit companies and organizations around the world and demanded that a cryptocurrency payment be made in exchange for the safe recovery of encrypted data.