Optimizing SIEM TCO: Smart Data Management Strategies
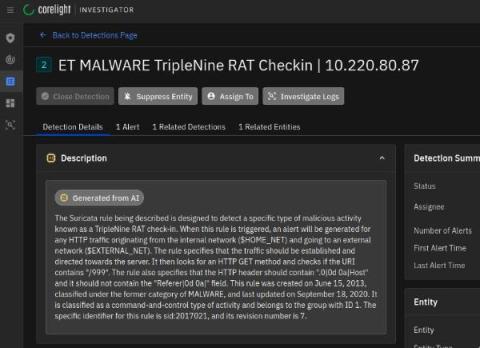
Let’s talk about a less discussed but critical aspect of Security Information and Event Management (SIEM) – data management. While the primary goals of SIEM include threat detection, regulatory compliance, and swift response, the backbone of these systems is log message ingestion and storage. The amount of machine data generated from various systems, applications, and security tools is staggering. Storing and processing this data can be costly and inefficient.