Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Access Management
Expanding Enterprise Attack Surfaces (EAS) and the increasing importance of Identity & Access Management
In the past five years, Enterprise Attack Surfaces (EAS) have evolved significantly. EAS refer to the various entry points that cybercriminals can exploit to gain unauthorized access to an organization's digital assets. With the increasing use of cloud-based services, the proliferation of connected devices and the growing reliance on third-party vendors, attack surfaces have become broader, more numerous and more complex.
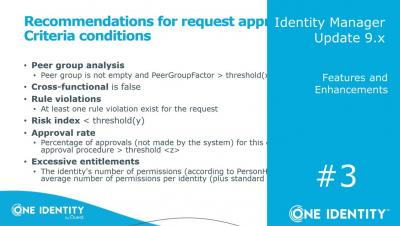
Identity Manager | Update 9.x #3 | Features and Enhancements
How to find and manage privileged accounts in Active Directory
When it comes to securing Active Directory, the first place to start is usually getting a handle on what currently exists - getting a ‘lay of the land,’ so to speak. In Active Directory, the admincount attribute can play a role in identifying privileged accounts. It’s not without its faults, however. In this blog, we will explore the admincount attribute in more detail and potential uses it may have for determining which accounts may have or had privileged access.
Privileged User Management vs Privileged Access Management: What's the Difference?
Bureau Veritas mitigates risk with OneLogin
Identity Manager | Update 9.x #2 | Connected System Module Enhancements
PAM Masterclass - Episode 4: Simplifying privileged session management
Making the Business Case for PAM Deployment
Privileged Access Management (PAM) solutions are designed to protect organizations from a variety of threats that target privileged accounts, credentials and access. These solutions help to secure, manage and monitor access to critical systems and sensitive data.