Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
Falco 101 - What is Falco?
7 Tips for Staying Safe on Social Media
The use of social media for both business and personal purposes has recently increased. Social media plays a vital role in allowing people from all over the world to communicate almost instantly; however, it is critical to manage your digital footprint as well as the security and privacy settings on your accounts in order for your personal information to be accessible only to you. Here are seven ways to help you stay safe on social media.
Learn OPA Policy with Guided Examples in Styra Academy
For many OPA users, they find it best to learn by example. That’s why we’re introducing a new Styra Academy Course, “OPA by Example!” For users that want to deepen their policy and Rego knowledge or better operationalize Open Policy Agent (OPA), this free course provides real-world examples to help you on your way.
What is a CISO? What They Do and How To Become One
Unlock the Power of Automation: Vulnerability Management
We’ve spoken extensively about the importance of taking a data-driven approach to Vulnerability Management. In short the efficiency and effectiveness of vulnerability management processes depend heavily on inclusion of threat intelligence for both prioritization and response activities. At any given time, only a small fraction of existing vulnerabilities are actively exploited or exploitable.
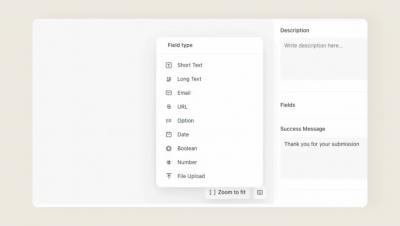
Forms
What Are JWTs?
JSON web tokens (JWTs) are an open standard for securely transmitting data as a JSON object between parties in a compact and self-contained format. Knowledge of JWTs is important because most modern systems and tools use them for secure, efficient and scalable authorization. Knowing about JWTs will also help you understand how third-party integrations with other software work.
How the Parkinson's Foundation Stays Secure With a Small IT Staff
At the Parkinson’s Foundation, we believe data security is a team sport, which is why we rely on everybody in our organization to follow best practices for protecting our content. Like most organizations, we have several layers of sensitive content, including some of our accounting and marketing files.