Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
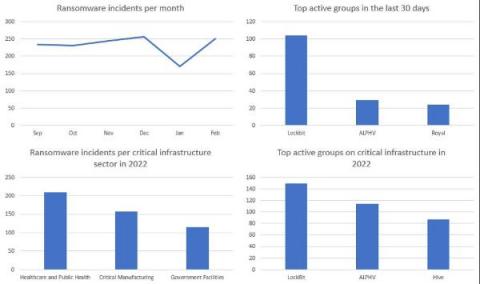
Detect the Most Common Ransomware TTPs to Prevent Attacks
In our new threat briefing, Forescout’s Vedere Labs details tactics, techniques and procedures (TTPs) commonly adopted by ransomware groups and provides specific mitigation recommendations. In addition to basic cyber hygiene practices, we recommend using Forescout XDR for extended detection and response. Its 1,500+ detection rules cover hundreds of the TTPs most commonly used by ransomware.
Expression DoS Vulnerability Found in Spring - CVE-2023-20861
Emotet Comeback: New Campaign Using Binary Padding to Evade Detection
Emotet is undoubtedly a very resilient botnet. Even though its operation was disrupted by Europol in January 2021, Emotet came back a few months later and continues to spread. In May 2022, shortly after Microsoft released new controls related to malicious macros, Netskope Threat Labs analyzed an Emotet campaign where they were testing a new delivery method, by using LNK files.
How to Handle AWS Secrets
In this blog post, we'll cover some best practices for managing AWS secrets when using the AWS SDK in Python.
What's Digital Rights Management (DRM)? Protecting Intellectual Property Today
What is a Dark Web Alert?
A dark web alert is a notification you receive when your personal information, such as your passwords, have been found on the dark web. Without a dark web alert, you won’t know when your personal information is posted on the dark web which is a threat to your identity and online security. Continue reading to learn more about dark web alerts, and how you can begin to receive these alerts and take action.
Save time fixing security vulnerabilities much earlier in your SDLC
Are you or your development team tired of using application security tools that generate countless results, making it difficult to identify which vulnerabilities pose actual risks? Do you struggle with inefficient or incorrect prioritization due to a lack of context? What adds insult to injury is that traditional CVSS scoring methods ignore critical details like software configurations and security mechanisms.
5 Key Components of Cybersecurity Hardening
Cybersecurity hardening is a comprehensive approach to keeping your organization safe from intruders, and mitigating risk. By reducing your attack surface, vulnerability is reduced in tandem. Hardening (or system hardening) considers all flaws and entry points potentially targeted by attackers to compromise your system.
VIN Cybersecurity Exploits and How to Address Them in 2023
Cybersecurity is no longer the exclusive domain of computers, servers, and handheld devices. As wireless connectivity grows, it makes many daily activities more convenient, but it also means that cars may be vulnerable to cyberattacks. Connected, Autonomous, Shared and Electric vehicles are starting to dominate the auto market, but they often carry significant cybersecurity risks.