Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
The security concerns of a JavaScript sandbox with the Node.js VM module
Were you tasked with building a product that requires the execution of dynamic JavaScript originating from end users? You might think building it on-top of Node.js VM module is a viable way to create a JavaScript sandbox. In this article, we’ll learn why that’s far from being a recommended approach and the security implications of doing so. Every now and then there’s a project that challenges the rudimentary and routine backend development. APIs? Message queues?
OWASP Kubernetes Top 10
One of the biggest concerns when using Kubernetes is whether we are complying with the security posture and taking into account all possible threats. For this reason, OWASP has created the OWASP Kubernetes Top 10, which helps identify the most likely risks.
5 Vulnerability Shifts You Need to Know for 2023
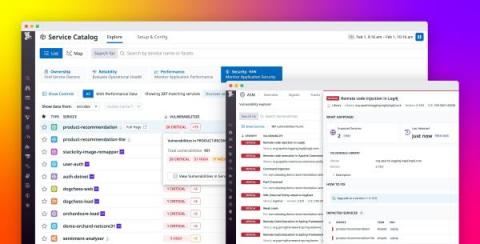
Code Intelligence Integrates with Jest to Enable Developers to Test JavaScript for Vulnerabilities
Gain visibility into open source vulnerabilities with Datadog Application Risk Management
Open source libraries have become an indispensable part of modern applications. Approximately 90% of organizations use open source software to support their services, but monitoring these dependencies can be difficult when environments run thousands of ephemeral services. The complex nature of modern applications, in combination with the challenge of keeping a competitive edge in a fast-moving market, can make it difficult for organizations to identify and remediate threats in a timely manner.
Ensure a secure IT environment with integrated network vulnerability management
When software isn't a "supply"
I was inspired to write this after reading a post from Thomas Depierre on Mastodon. The post touched on something that’s been troubling me recently. When it comes to software security, we spend a lot of time talking about the software supply chain and related concepts, such as the software bill of materials (SBOM). This metaphor comes from an industrial lexicon. People who are used to talking about economies and how manufacturing works are familiar with the idea of supply chain.
The dangers of setattr: Avoiding Mass Assignment vulnerabilities in Python
Mass assignment, also known as autobinding or object injection, is a category of vulnerabilities that occur when user input is bound to variables or objects within a program. Mass assignment vulnerabilities are often the result of an attacker adding unexpected fields to an object to manipulate the logic of a program.