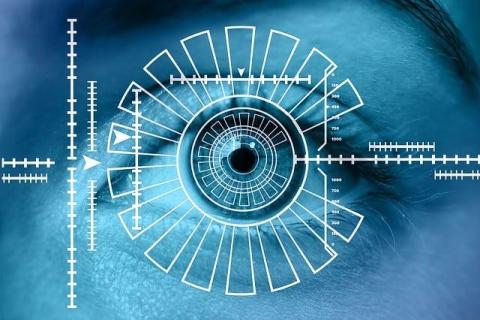
What technology is reliable to provide a high quality biometric recognition service?
Biometric Recognition Service is the process of identifying individuals with unique physical characteristics, offering high security. Advanced biometrics technology relies on scanning fingerprints, recognizing faces, and identifying voices or scanning irises, and guarantees accurate identification while minimizing errors.