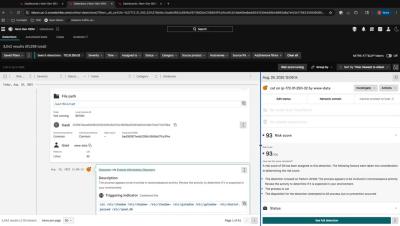
Securonix - Breach Ready. Board Ready. AI-Powered.
Security teams today are expected to do it all. Stop threats faster. Prove value to the board. Scale with fewer resources. Securonix makes it possible. Breach Ready means unified detection and response with up to 60 percent faster time to containment and 50 percent less analyst workload. Board Ready means 193 percent ROI, a six-month payback period, and reporting that drives strategic decisions. AI Powered means modular agents that cut false positives by 90 percent and automate triage with precision, keeping your team in control. This is modern security. This is Securonix.