Exposing Salt Typhoon on the network using the PEAK Threat Hunting Framework
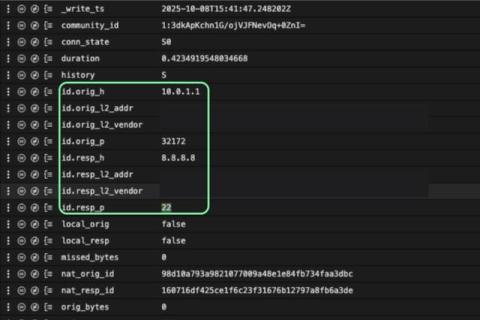
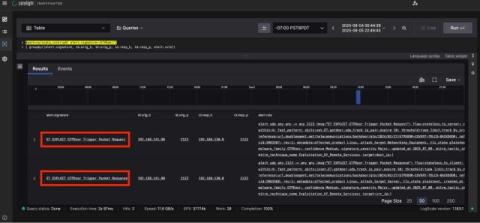
How do you find an adversary who lives where you can't easily look? A recent CISA advisory on the state-sponsored actor "Salt Typhoon" highlights this exact challenge. These actors aren't just breaking in; they're moving in. They persist on network edge devices like routers and firewalls—critical infrastructure that often sits outside the view of traditional endpoint security. From this vantage point, they capture traffic, steal credentials, and plan their next move.