Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cloud Computing Security: A Primer
Gartner forecasts that worldwide public cloud end-user spending will grow 23% to USD 332.3 billion in 2021 as cloud technologies become mainstream. As cloud computing architectures continue to become more prevalent, “cloud native” has become a popular buzzword. But what exactly does “cloud native” mean and what impact does it have on security? How exactly do you secure all these cloud native applications?
Trends in Cloud Adoption: Why Cloud Computing is on the Rise
In this post, I’ll answer one question: Have we reached the tipping point for cloud proliferation? According to the report, the answer is yes. ESG surveyed 500 IT and security professionals working in the security operations center (SOC) chain of command at organizations with more than 1,000 employees in North America and Western Europe in Q1 of this year.
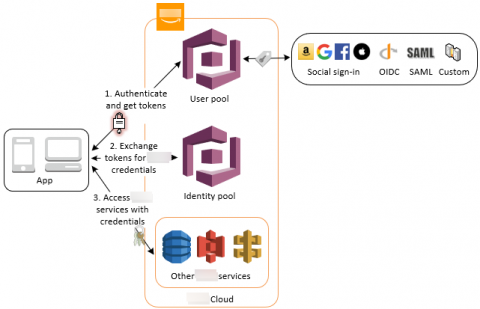
How does AWS IAM role, STS and Identity Pool work with each other.
We talked about IAM in the past 3 posts, identities in IAM, manage users privilege as an IT person and control privilege boundaries. We also talked about how applications use AWS Cognito Identity Pool to get AWS temporary credentials to access AWS resources in early posts of “What I wish I could have learned before starting using AWS Cognito” and “Authentication and authorization with AWS Amplify under the hood”.
Difference between Agent-based and Network-based Internal Vulnerability Scanning
Technology evolution is the only constant in our lives these days. Sometimes, an existing approach can go a long way in addressing problems, while other times, a new approach needs to be adopted to get the work done. Let’s talk about vulnerabilities; internal networks and software can be riddled with loopholes, which can expose them to breaches and data leaks, paving the way for hackers to have an easy ride.
Amazon RDS Restore Guide
Glaring Gap in Open Source Security: Veracode Finds 80 percent of Libraries Used in Software Are Never Updated
Introducing the World's First Modern Cloud-Based SecOps Platform: Splunk Security Cloud
To say that the past year presented its fair share of cybersecurity challenges to the InfoSec community would be a drastic understatement. The rapid migration to remote work at scale left 80% of CIOs unprepared, and SecOps teams struggled to confront the evolving threat landscape with disparate toolkits and skill sets. Not to mention that as more organizations shifted to hybrid and multi-cloud environments at scale, cloud complexity (and cloud-based threats) skyrocketed.
The Top 5 Vendor-Neutral Cloud Security Certifications of 2021
Most organizations have already begun their shift to the cloud. In its Cloud Computing Survey 2020, for instance, International Data Group (IDG) found that 81% of respondents had at least one workload or segment of their computing infrastructure in the cloud. That percentage could grow by the end of the year, as IDG found that 32% of total IT budgets will go to cloud computing—up from 30% in 2018.
Voice-Activated Device Privacy: What You Need to Know
When it comes to evaluating technology in the home, there seems to be no shortage of new devices and shiny gadgets, mainly part of the Internet of Things (IoT), to discuss. Unfortunately, there seems to be no shortage of security issues to consider regarding these same devices, either.