Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Right Steps to SASE: Extend Zero Trust to Data Protection and Private Access
The following is an excerpt from Netskope’s recent book Designing a SASE Architecture for Dummies. This is the fifth in a series of seven posts detailing a set of incremental steps for implementing a well-functioning SASE architecture. Now that your organization is smarter about its traffic, able to see what’s going on, and able to enforce policies to secure its data, you can realize the promise of a remote-first workforce.
Bridging the Network-Security Divide with SASE Thinking
The many business benefits made possible by digital transformation are undoubtedly making waves across industries. Data is the raw material that drives smarter decision-making, and as such, drives value for organizations, but things quickly get challenging when you start to consider how all that data will be used—and who has access to it, when.
Cloud Threats Memo: Illustrating Big Risks in the Shift to Remote Working
The exploitation of traditional remote access technologies is reaching new records. That, in a nutshell, is the main finding of Nuspire’s Threat Landscape Report Q1 2021. The report, sourced from 90 billion traffic logs during Q1 2021, looks at a range of events such as malware activity, botnet activity, exploitation activity, and remote access. The remote access section probably best illustrates the risks posed by the sudden shift to remote working.
Scan for AWS CloudFormation misconfigurations with Snyk IaC
We’re excited to announce the launch support for AWS CloudFormation in Snyk Infrastructure as Code. In our recent Infrastructure as Code Security Insights report, we found that 36% of survey participants were using AWS CloudFormation (CF) as their primary infrastructure as code tool of choice. Using Snyk Infrastructure as Code, you can now scan your CF YAML or JSON templates against our comprehensive set of AWS security rules.
Understanding Mobile Application Penetration Testing Methodologies
Mobile Application Penetration Testing Methodology as a security testing measure, analyses security perimeters within a mobile environment. Derived from the traditional concept of application security methodology, its main focus lies on client-side security and it broadly puts the end-user in control. By conducting penetration testing, companies can gain insights into the source code’s vulnerabilities, bottlenecks, and attack vectors beforehand.
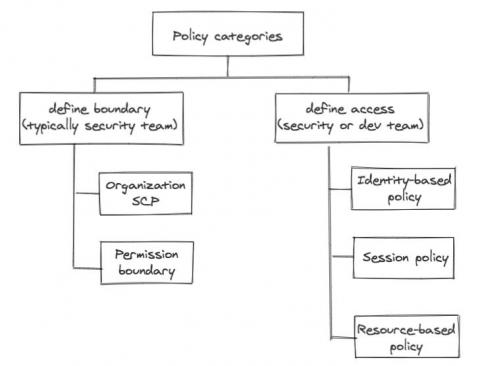
AWS IAM in a layman's terms
We alluded in one of our previous posts that the development team will own a lot of responsibility defining application related resource access control, simply because the dev team owns the infrastructure as code (IaC) responsibility themselves. No matter how security-savvy and security-educated a development team is, the central security team still needs some control, some kind of “trust but verify”.
Netskope Named a 2021 Gartner Peer Insights Customers' Choice for Secure Web Gateway
At Netskope, one of our core values as a company is that customers are always our number one priority. We know that technology projects are rarely easy undertakings and it’s our job to be there for our customers and for them to know we have their backs. With that in mind, we are excited to announce that Netskope has been recognized as a Customers’ Choice in the June 2021 Gartner Peer Insights ‘Voice of the Customer’: Secure Web Gateway.
Advancing SBOM standards: Snyk and SPDX
Many people will have heard of the SPDX project through the work on the SPDX License List. This list of canonical identifiers for various software licenses is used in a huge range of developer-focused software, from Snyk to GitHub. But the SPDX project, which is part of the Linux Foundation, has a much broader focus on providing an open standard for communicating software bill of material information.
Cloud Threats Memo: Takeaways From the Q1 2021 Phishing Activity Trend Report
The Anti-Phishing Working Group (APWG) has just released its Phishing Activity Trend Report for Q1 2021. The first findings are easily predictable; the dispersion of the workforce is pushing phishing attacks to new records: just in January 2021, the APWG detected 245,771 unique phishing sites, the highest number reported so far.