Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Best Practices for Implementing Cloud Migration Security
As modern businesses increasingly rely on cloud services, securely migrating data to the cloud has become crucial. Effective cloud migration allows organizations to leverage external expertise and resources while maintaining data integrity and compliance. This guide provides a comprehensive understanding of secure cloud migration, best practices, essential security measures, and successful real-world examples to help businesses benefit from these practices without compromising data security.
Securing Your Sensitive Data: Top 7 Cloud Migration Strategies and Best Practices
Cloud migration refers to the process of moving data, applications, and other business elements from on-premise data centers to a cloud computing environment. This transition is crucial for modern businesses aiming to enhance their operational efficiency, scalability, and flexibility. Cloud migration offers numerous benefits, including cost savings, improved performance, and the ability to leverage advanced technologies like AI and big data analytics.
Friday Flows Episode 30: Normalize Alerts with Tines AI and create Cases AI
FRIDAY FLOWS Episode #30 - Normalizing Alerts using Tines AI & Creating Cases In today's episode, Michael Tolan takes us through a workflows where we're leveraging the new Tines AI Action to normalize multiple alerts and create cases in our native Case management. As always, our free Community edition is in the comments and we'd love to hear what you thought of today's episode in the comments.
MLOps & the Role of GenAI in Securing the Software Supply Chain
Artificial Intelligence and Machine Learning have hit the mainstream – particularly the use of Gen AI and LLMs to help organizations automate manual processes and analyze data at machine speed with dramatic results. How can ML and Gen AI help DevOps teams better secure the software supply chain? As the volume of code grows exponentially, these evolving technologies offer new, more efficient means to secure, deliver and scale software – but with accompanying risks that must be mitigated.
8 Stages of the AI "Emotional Rollercoaster"
Feelings are running hot right now when it comes to generative AI (GenAI). Within the business community, many employees (and execs) are nervous with excitement and anticipation. Others are more fearful and skeptical of how this “thing” will play out, which leads us to an important question: Are enterprises too emotional when it comes to adopting nascent technologies?
AI in cybersecurity 101: Bridging the skills gap
“Four million workers wanted. Immediate start. Must have knowledge, experience and an ability to be in several places at once.” If the cybersecurity industry posted a job ad, it would sound something like this. That is the current reported size of the talent shortage, with “little optimism that the supply will catch up.”
AI Treason: The Enemy Within
tl;dr: Large language models (LLMs) are highly susceptible to manipulation, and, as such, they must be treated as potential attackers in the system. LLMs have become extremely popular and serve many functions in our daily lives. Every reputable software company integrates artificial intelligence (AI) into its products, and stock market discussions frequently highlight the importance of GPUs. Even conversations with your mother might include concerns about AI risks.
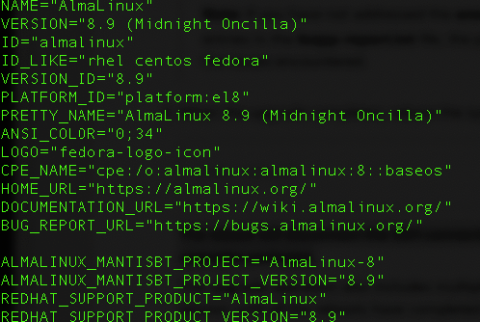
Ubuntu 20.04 vs 22.04: Comparing features and performance
Jump to Tutorial Ubuntu is a popular Linux distribution that has been adopted by many system administrators, developers, or everyday users who are searching for a robust and open-source operating system. Each version of Ubuntu brings new features, improvements and sometimes there are certain changes in system requirements.
The Most Comprehensive Introduction to the Six PCB Applications
Currently, PCBs are available in various types, including single-sided, double-sided, and multilayered PCBs. Some PCBs are rigid, while others are flexible. Some have a combination of both rigid and flexible parts. As mentioned earlier, PCBs have widespread applications. In this article are six of the most common PCB applications.