Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SOC 2 Compliance for SaaS: How to Win and Keep Client Trust
The Software as a Service (SaaS) industry has seen both great expansion and notable downturns in recent years, with key market shifts redefining the landscape.As companies adapt to the shifting SaaS landscape, SOC 2 Compliance for SaaS has emerged as a key priority—not just as a checkbox for security, but as a signal of trustworthiness and a commitment to protecting customer data in an increasingly cautious market.
From Data to Defense: How AI and Governance are Rewriting the Rules of Compliance and Security
The digital age has introduced both immense opportunities and unprecedented challenges for businesses. Data is a powerful asset, yet managing its governance, security, and compliance requires intricate strategies and solutions. Leveraging artificial intelligence (AI) in these areas has become a game-changer in transforming how organizations of all sizes approach their data capabilities.
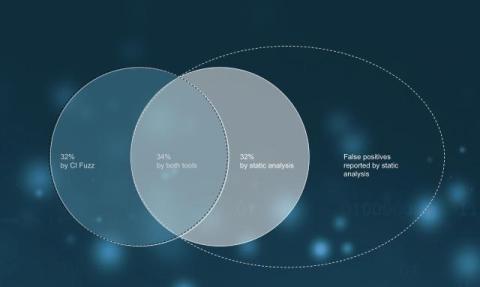
Automotive Supplier Finds 32% of Bugs Through Fuzz Testing
An automotive supplier employs static analysis and Code Intelligence's Fuzz Testing to assess software within a separate business unit. The project comprises 10 million lines of C code, adhering to Classic AUTOSAR standards.
Introducing Zenity for ChatGPT Enterprise
More than 80% of Fortune 500 companies rely on ChatGPT Enterprise, not just as a productivity tool, but as a platform for building custom GPTs, leveraging knowledge files, and enabling collaboration through Canvas. As AI Agent adoption accelerates across every corner of the enterprise, business users are innovating faster than ever, often without security oversight.
CrowdStrike Falcon for IT Adds Endpoint Automation to Advance SOC Transformation
Today, CrowdStrike is releasing automated baseline enforcement and remediation in CrowdStrike Falcon for IT to secure misconfigured devices and consistently address vulnerabilities across endpoints. Operators can now centrally manage and enforce endpoint configurations across platforms to support security and compliance efforts.
Customer Success Story - Tanium Patch - Tanium Tech Talks #124
Meet a Tanium administrator who has achieved great success with Tanium Patch and Deploy in a 24x7 business environment.
Introducing Always-Accurate Endpoint Collection with Forward Enterprise
For most enterprises, endpoint visibility remains one of the most elusive elements of network security. Devices connect, disconnect, or move constantly, making it nearly impossible to keep an accurate inventory with traditional tools. Without a clear picture of all endpoints—laptops, printers, IoT devices, and more—security and compliance teams are often flying blind. That changes with Forward Networks’ new endpoint collection feature.
Monitoring Workers with AI? We're Not OK With That.| Razorthorn Security
AI surveillance in the workplace is rising fast — but what about data rights, regulation, and unions? Jemma breaks down the ethical red flags.