Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Monitoring Transaction Log Files for PCI compliance
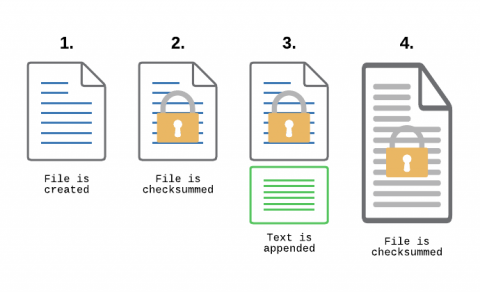
File Integrity Monitoring, aka as FIM, is a must-have feature for anyone in charge of security. With FIM, one can detect when a critical file, such as a file that belongs to the Operating System, or a key configuration file, is changed. In most cases, configuring FIM is straightforward: If the file changes then generate an alert.
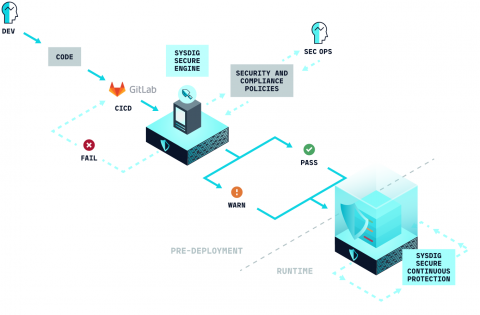
Image scanning for GitLab CI/CD
Scanning a container image for vulnerabilities or misconfigurations on your GitLab CI/CD using Sysdig Secure is a straightforward process. This article demonstrates a step-by-step example of how to do it. The following proof of content showcased how to leverage the sysdig-cli-scanner with GitLab CI/CD. Although possible, this procedure is not officially supported by Sysdig, so we recommend checking the documentation to adapt these steps to your environment.
CrowdStrike Enables Federal Departments and Agencies to Meet CISA Operational Directive 23-01
In support of the Executive Order on Improving the Nation’s Cybersecurity, the Cybersecurity and Infrastructure Security Agency (CISA) recently published a Binding Operational Directive (BOD) 23-01, designed to improve cybersecurity for the Federal Civilian Executive Branch (FCEB) enterprise and their respective unclassified assets.
Introducing GraceWrapper, TA505's sophisticated post-exploitation enabler
Since its inception almost a decade ago and the MirrorBlast campaign, the threat actor group known as TA505 has continued to plague the financial, retail and restaurant sectors.
12 Essential ways to improve your website security
In today's digital age, a business website is essential for success. Not only does it provide potential customers with information about your products or services, but it also allows you to connect and engage with them directly. However, simply having a website is not enough. To ensure that your site is effective and safe, you need to make sure that it has all the necessary security features. In this article, we will discuss twelve security features that every business website must have.
7 Key Measures of an Insider Threat Program for the Manufacturing Industry
Leveraging Microsoft Teams webhooks to create a Tines chatbot
Microsoft requires users to leverage the Microsoft Developer Portal to create new Teams applications, such as chatbots. At Tines, we thought it might be helpful to provide instructions for alternative options if you don't want to create a chatbot in the portal. For those who would prefer to send messages directly to a Teams channel instead of configuring a chatbot, Microsoft Teams can receive messages in a channel via a webhook.
The Riskiest Connected Devices in Enterprise Networks
The growing number and diversity of connected devices in every industry presents new challenges for organizations to understand and manage the risks they are exposed to. Most organizations now host a combination of interconnected IT, OT and IoT devices in their networks that has increased their attack surface.
Introducing 1Password 8 for Apple Watch
Your most precious data is now securely accessible from your most personal device. The all-new 1Password for Apple Watch offers customizable access to nearly anything in your 1Password account, with full support for complications and the same intuitive experience you know and love.