How Third-Party Development Partners Become Your Biggest Security Liability
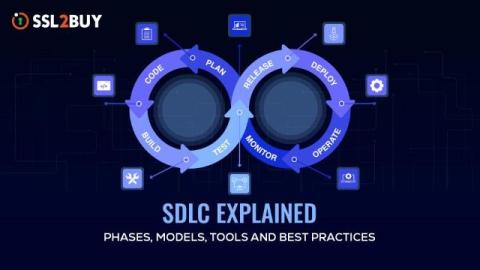
Third-party development partners offer real advantages: faster delivery, specialised expertise, and lower costs than building an in-house team. They also expand your attack surface in ways most organisations never fully account for. When an external team builds or modifies your systems, they bring with them their own tools, practices, access levels, and vulnerabilities. The question is not whether that creates risk. It is whether your organisation is managing it deliberately or leaving it to chance.