Combat Cybercriminals With Sound Office Policies
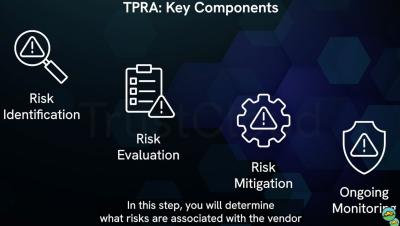
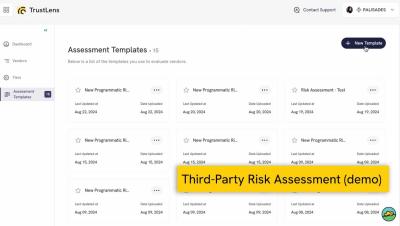
According to the FBI, cybercrime cost American businesses $12.5 billion in 2023. More worrying was that this was a 22% increase from the previous year, even though there were fewer complaints in 2023. Just over 60% of those losses were due to phishing emails, showing that humans are the weakest link. As a result, you need to ensure that your office policies are on point. In this article, we'll look at where to focus your efforts. We'll discuss physical security, third-party vendors, and training your team.